Outcome-Driven Metrics and Protection Level Agreements
No single cyber security control can protect against every situation. The concept of defence-in-depth anticipates multiple independent security controls operating in concert to protect you across the attack sequence. Ransomware readiness or resistance is best achieved when the effectiveness of these security controls is maintained across each of the prevention, containment and recovery phases.
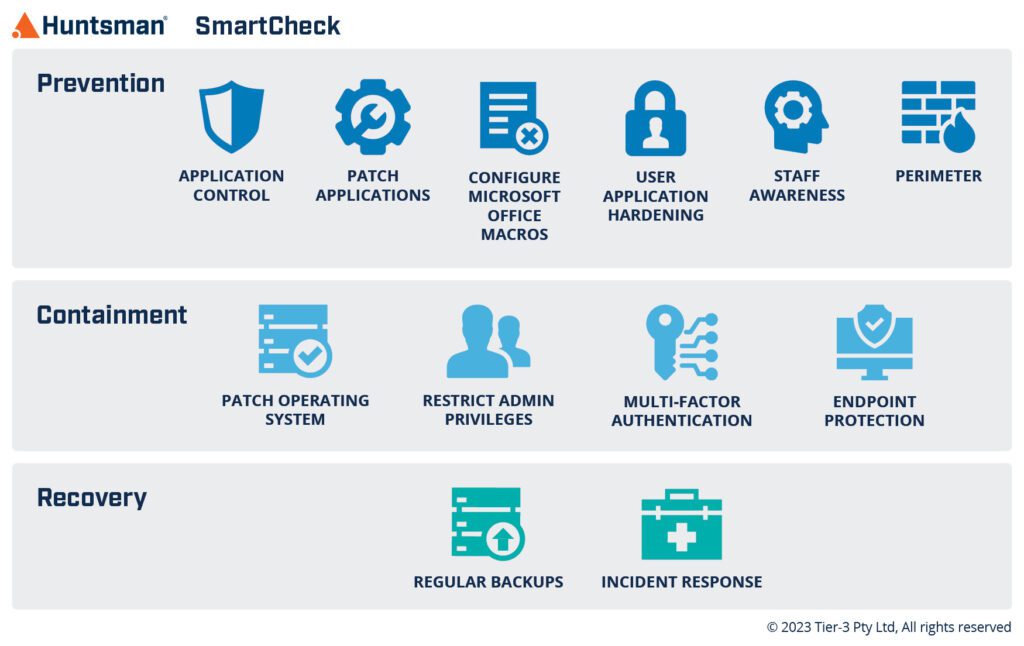
Accurate, reliable and quick measurement to maintain the effectiveness of the 12 Safeguards ensures the risk of a successful ransomware attack is kept to a minimum. Beyond your annual audit, SmartCheck can be used on-demand to quickly provide comprehensive ransomware readiness reports as and when required.
Only approved software should run on a computer system. This safeguard supports securing your systems by limiting what can run on devices across your organisation.
Macro and document settings need correct configuration. This safeguard checks macros and settings to protect against malicious code.
Building an ongoing understanding by staff about cyber security threats, and mitigation strategies that minimise cyber-attacks, is vital. This safeguard is a checkpoint for ongoing staff awareness.
Applications must be regularly patched or updated to prevent intruders exploiting known vulnerabilities. This safeguard supports the identification of vulnerabilities and the application of relevant patches in a timely manner.
Effective security policies limit user access to active content and web code. This safeguard supports the implementation of application and browser controls.
Appropriately configured and regularly updated, perimeters/firewalls can limit access to, and use of, certain computer systems. This safeguard defends your network against unauthorised traffic.
Fully patched operating systems are vital across every endpoint. This safeguard reduces the likelihood of malware or ransomware spreading across the network.
Requires multiple independent credentials to verify a user before they gain system access. This safeguard supports the management of user access (including remote users) to high sensitivity accounts and systems.
Best-practice limits admin privileges, by allowing only those staff needing system access to do so, for specified purposes. This safeguard limits the number of users who can make significant changes to your systems.
Anti-virus software is a vital part of any cyber security strategy. This safeguard supports the coverage of anti-virus software across every device within your organisation.
Securing data and system backups off-site, and testing recovery processes is crucial. This safeguard ensures important data, systems information and configurations are backed up and retained in a secure manner.
Validating that incident management plans exist and are tested. This safeguard supports planning for a worst-case scenario and the use of your incident management playbook.
Read by directors, executives, and security professionals globally, operating in the most complex of security environments.