Outcome-Driven Metrics and Protection Level Agreements
Learn how privacy and security considerations could be ignored in the rush to open banking.
Open banking is the recent sentiment in the financial services industry to embrace the concept of offering their data as a platform for other fintech businesses to use in their own product offerings. The Australian federal government has announced that an Australian open banking regime will be implemented from July 2019, where banks and financial bodies have to make their clients’ information available in a “useful digital format” when requested by customers. This means the banks must provide direct access to that information, encouraging a wave of innovation and new product launches to make use of this newly accessible data set.
Like all open data initiatives, the success of open banking will be determined by the pervasive adoption of rigorous security and privacy controls, which some believe are being ignored in the rush to market. Let’s take a look at what fintech companies must consider when designing services to leverage these open banking standards and keep their clients’ data confidential.
The government is mandating open banking laws that compel Australian banks to reveal customer data across 27 different deposit and lending products. However, banks will not have to provide access to the data they have transformed for analytical purposes, since this data is considered internal to the bank and not the raw data, which is owned by the consumer.
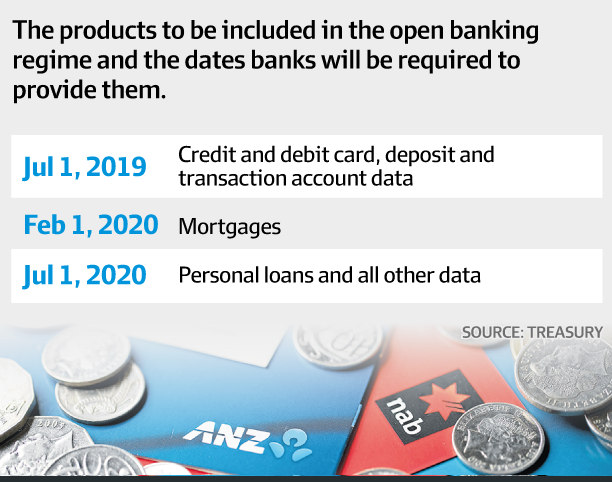
The products included in the open banking laws are shown in Figure 1 below:
Figure 1 Open banking laws mandate banks provide open access to these products
Data61 is mooted as the initial steward of the open banking technical security standards. What we do know is that any organisation that wants access to the data will need to be accredited – accreditation hasn’t been defined, but it’s clear that whatever form it takes, it will involve rigorous information security and privacy. Interestingly, criticism of the government’s approach to open banking has suggested that too rigorous an approach to information security will only serve to delay its implementation.
The risks introduced by open banking are many, however, most criticism focuses on the fact that customer data will be stored in many different locations, thus the end-user loses control over the release of their information, increasing the attack surface and their exposure to identity theft. Cyber criminals will see this as a primary target, worth spending time on researching and building bespoke attacks, since the value of the data set is enormous when sold on the black market. There are a variety of things that fintech companies can do right away to adopt good security practice, without having to wait for the ACCC to publish their standards.
Firstly, risk management is the focus of all information security initiatives, so fintech companies should adopt a governance model that incorporates risk management and compliance monitoring to allow them to prioritise their security efforts. The controls specified by the regulators will likely equate to those in existing standards anyway, such as those introduced by Australian Prudential Regulation Authority (APRA) earlier this year. APRA wants a dedicated standard for cyber security that applies to all financial services companies, so this will likely apply to open banking data users too. To get a head start, adopting a standard such as this will mean fintech companies can put the governance, risk and compliance (GRC) control in place during the architecture and design phase of their service development, which makes intrinsic security controls (operational controls) much more likely to succeed.
A successful GRC implementation requires all levels of strategic, tactical and operational security controls to be integrated together, underpinned by a reporting capability where the security management team can monitor everything from policy compliance to network security event correlation and automated threat detection. The focus for this kind of activity should be on developing a Security Operations Centre (SOC), which tends to concentrate the security efforts into something tangible that the board can understand. However, this SOC doesn’t have to cost vast amounts of money or even be staffed internally, since companies have options to outsource their operational security capability to an expert organisation that can monitor systems 24x7x365.
Whether the SOC is insourced or outsourced is neither here nor there, since it’s the requirements the SOC delivers against and the assurance it is providing that service that’s important. The SOC should be able to address the need for real-time threat detection, automated threat verification, tuning the monitoring capability and event correlation, and analysts should be working to remove false positives.
The most important aspect of building (or outsourcing) a SOC is in defining the requirements of what it will monitor. The SOC should work back from the desired outcome – in this case protecting customer data from falling into the wrong hands, and then rules will be developed based on real-world attack profiles. If an attacker might try to compromise a back-end administrator’s account, for example, then monitoring the administrator’s behaviour would make sense. Behavioural anomaly detection needs to be built into the SOC requirements and tuned against the normal behaviour of the service management team, so that anything odd or out of the ordinary is immediately flagged for further investigation. Furthermore, automation will help reduce the time required to identify and contain a threat, where one of these anomalies can then be further investigated, maybe through DNS lookups, checks against threat intelligence or cross-checks with IP addresses, subnets and geolocations.
Open banking introduces yet more concerns for Australian citizens around their privacy and unless the government enforces rigorous security controls and compliance requirements for fintech companies, there is a real risk that our financial data will fall into the wrong hands.
Fintech companies who want to do the right thing don’t have to wait to be told how to secure user data – it’s not like this is a new thing for businesses to do. Instead, they should look to existing standards, such as APRA’s cyber security guidelines, and introduce governance, risk and compliance measures to ensure data security is built into their products from inception.
Building an operational security capability is something that even the smallest fintech start up can do, especially if they work with a managed security service provider to scale up this capability as the business grows. Most MSSPs have scalable solutions that match this requirement, so if the fintech company starts with a comprehensive list of security requirements from the outset, security can become just another facet of their value proposition.
Continuous monitoring, reporting, the ability to handle API or machine-to-machine transaction flows and rapid (automated or system-assisted) incident detection, verification and response are all vital cyber security capabilities that Huntsman Security delivers in support of Open Banking.
Whilst Australian Open Banking will not take effect until July 2019, European Open Banking legislation became effective in the EU in January 2018. To explore how this works, you can visit our PSD2 Opening Banking page.
Read by directors, executives, and security professionals globally, operating in the most complex of security environments.