Outcome-Driven Metrics and Protection Level Agreements

This blog post “CMMC – Achieving a Level 4 SOC’’ is the sixth in a series on Cybersecurity Maturity Model Certification (CMMC) – a US Department of Defense (DoD) initiative that imposes requirements on contractors and subcontractors to help safeguard information within the US defense supply chain.
This post provides insights into how you can achieve Level 4 maturity across the enterprise, focusing on the proactive elements of security controls you need to demonstrate to achieve this lofty status.
Each level of the CMMC’s maturity model represents a step-change in how security controls are deployed and managed across your business. Maturity begins with Level 1, where the control is “performed,” meaning carried out to some extent, but with no evidence of consistency or completeness. As you move through Level 2, you begin documenting all your practices and procedures, then finally at Level 3, you are fully managing controls across the enterprise. Level 3 is a reasonable goal for many organisations starting on this journey, and many will stop there, thinking this is enough. Yet, modern cyber criminals and nation-state adversaries don’t care how mature you are, if they can find that one chink in your armour, they will still exploit it.
At Level 4 maturity, you are turning to more proactive security controls, where your protection levels are working to defeat the more advanced attacks of Advanced Persistent Threats (APTs) such as nation-states and highly sophisticated criminal gangs. Security practices enhance detection and response capabilities and may align your security operations approach to MITRE’s ATT&CK Framework. This approach helps you gauge the efficacy of controls against attacker tactics, techniques and procedures, so you can fully understand and monitor how effective they are against the attacks against which they defend.
Let’s look at one of the CMMC domains at Level 4 to understand what’s required.
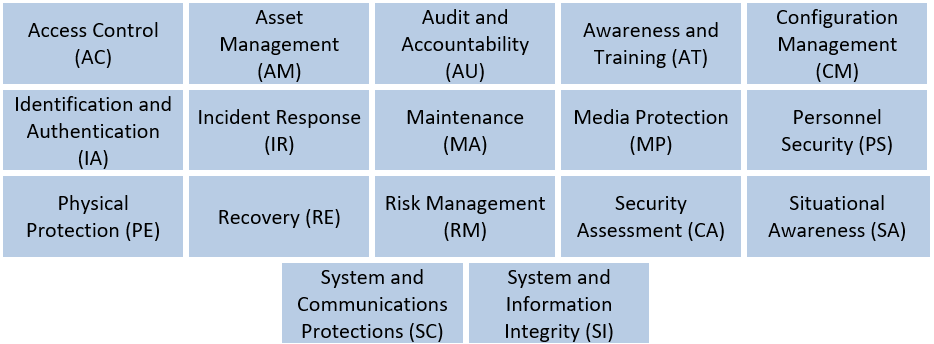
CMMC Domains
At Level 3, you establish the ability to capture logs from the enterprise, and you review those logs using a central function, such as your Security Operations Centre (SOC). The SOC likely has (and needs) investigative tools, such as a Security Information and Event Management (SIEM) platform. You’ll be alerting on suspicious activity, correlating events against known attack tactics, techniques and procedures, and comprehensively reporting on activity.
Level 3 also demands your SOC is mature and is doing a reasonable job at protecting your organisation from basic cyberattacks, especially opportunistic attacks and those related to random infections from phishing and malicious website infections.
Level 4 introduces extensive automation across the threat management lifecycle, from log analysis to incident response and reporting. Analysis occurs at an organisational level, using trends and graphs to detect patterns denoting the tactics, techniques and procedures of attackers. These patterns may be undetectable at the local machine level, so requires advanced tools, such as artificial intelligence, machine learning and behavioural analytics. By introducing automation and deep learning across the enterprise, your threat management activity transitions from reactive to proactive. Threat models and behavioural patterns show you your adversaries actions earlier in the attack lifecycle, so you can respond sooner, thus reducing the overall impact to the business.
Automation helps improve how quickly you detect an attack, and the speed of response, both of which reduce the harm the attacker causes. You boost detection speeds by automating event correlation using special rules that denote attack patterns – there are correlation rules and SIEM products that provide this capability. Automating threat verification can boost response time, which more advanced SIEM platforms can do as well. Both activities require threat models, so you must understand your organisation’s business and systematically develop these models to understand how an adversary would target your assets. You then establish correlation rules to detect those kinds of patterns and raise an alert with the SOC team.
Automating the response is the final step after verifying the threat. You must be confident the threat is real before automating actions to block traffic or remove systems from the network, so checking attacks are legitimate is an essential step when trying to build trust with the business. For Level 4, you must act to block attacks. These actions do not have to be comprehensive; instead, they should slow the attacker down and ensure you have time to conduct a more extensive investigation.
For example, a malicious insider attempts to copy records from your customer database to their local computer. Your threat model dictates that a query containing more than five database records at a time requires investigating. A string in the event log records the number of database records requested in one query. When the SIEM processes the event, it immediately raises an alert with the analyst. The analyst now begins the incident response process. However, to limit harm while the incident response team mobilises, the SIEM might quarantine the endpoint where the data was copied to, lock the user account and log the user off. It might also send a request to the IT team to confiscate the device, of course, ensuring a security guard accompanies them.

As you can see from this example, reaching Level 4 maturity requires a deep understanding of your business and systems, as well as a deep understanding of the threat models that represent how attackers will target and steal your information. However, you will also need to use sophisticated tools within your SOC to automate detection, threat verification and response actions, all of which require a SIEM with SOAR capabilities – Security Orchestration, Automation and Response.
If you want to learn more about how you can automate your threat detection and incident response, contact us today.
Read by directors, executives, and security professionals globally, operating in the most complex of security environments.