This blog post ‘How to mature Audit and Accountability’ is the third in a series on Cybersecurity Maturity Model Certification (CMMC) – a US Department of Defense (DoD) initiative that imposes requirements on contractors and subcontractors to help safeguard information within the US defense supply chain.
You can read the first two blog posts here and here. In this post, we take a look at the security disciplines of Audit and Accountability and how organisations can fulfil the CMMC requirement to achieve a more robust approach to governance and compliance.
Individual accountability
Individual accountability is a concept that lies at the heart of a good governance and compliance model, since without evidence to trace actions back to specific users, there is no way to determine who did what, whether that person should have done it; and there is no way to enforce rules or disciplinary actions without proof.
Most modern computer systems can record every single action that occurs. In Microsoft Windows, a blend of group policy settings and System Access Controls Lists (SACLs) supports this. You would set the group policy to record the kinds of events you are interested in, then apply SACLs to objects, such as the files, folders and the registry, then users accessing those resources will result in the system generating an event based on the group policy audit setting.
For example, if success auditing is enabled, a log entry is created when any user accesses a file with a matching SACL. Similarly, if you enable failure auditing, a log entry is recorded when a user unsuccessfully attempts to access a file with a matching SACL.
It’s important that anyone setting up the security architecture for a business understands the importance of individual accountability so they can deploy systems capable of complying with the requirements. These requirements should influence decisions such as how you structure your username convention, if you use location-aware authentication and multi-factor authentication, since all of these attributes of a user’s session can digitally tie them to the actions they take on your systems. At a minimum, you should ensure your audit system collects user IDs, source and destination IP network addresses, and that the system timestamps associated with the actions being recorded, so you know who did what, from where and when.
Additional attributes, such as machine ID and specific details relating to the activities are all useful in building a picture of what happened on your systems, so in the event of a breach you can better trace what happened. In many cases, this level of auditing helps exonerate users suffering credential theft since you can match patterns of access from their normal behaviour against the breach to prove the breach came from elsewhere.
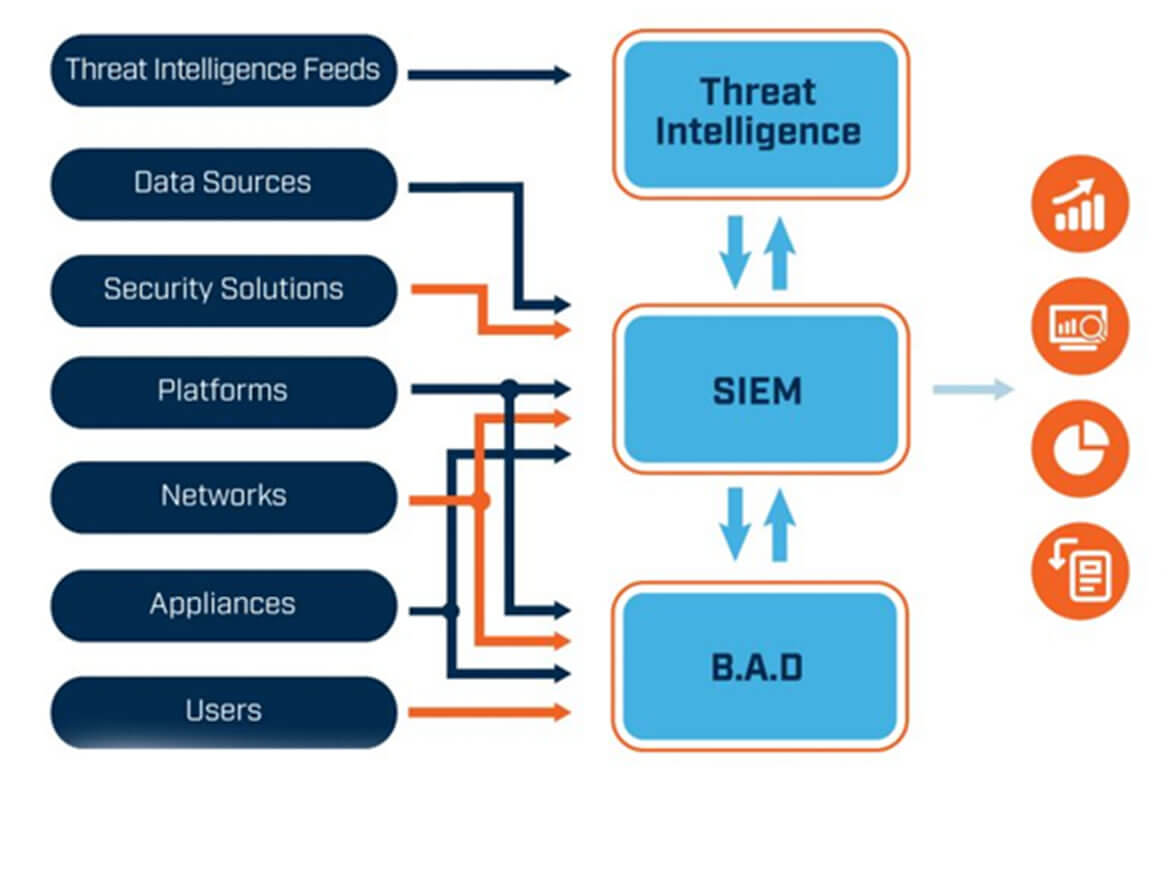
Aggregate and store logs for analysis with SIEM
Every audit log your systems generate can become useful in an investigation, however, one of the biggest challenges digital forensic investigators face is that those logs are usually distributed across many hundreds (or even tens of thousands) of systems, crossing user access devices, servers, cloud-based systems, network devices and applications, all of which create their own logs. Furthermore, the structure of audit logs across multiple sources is never consistent, so an event created on a Microsoft Windows 10 computer will look entirely different to that of an event created inside an Oracle database application.
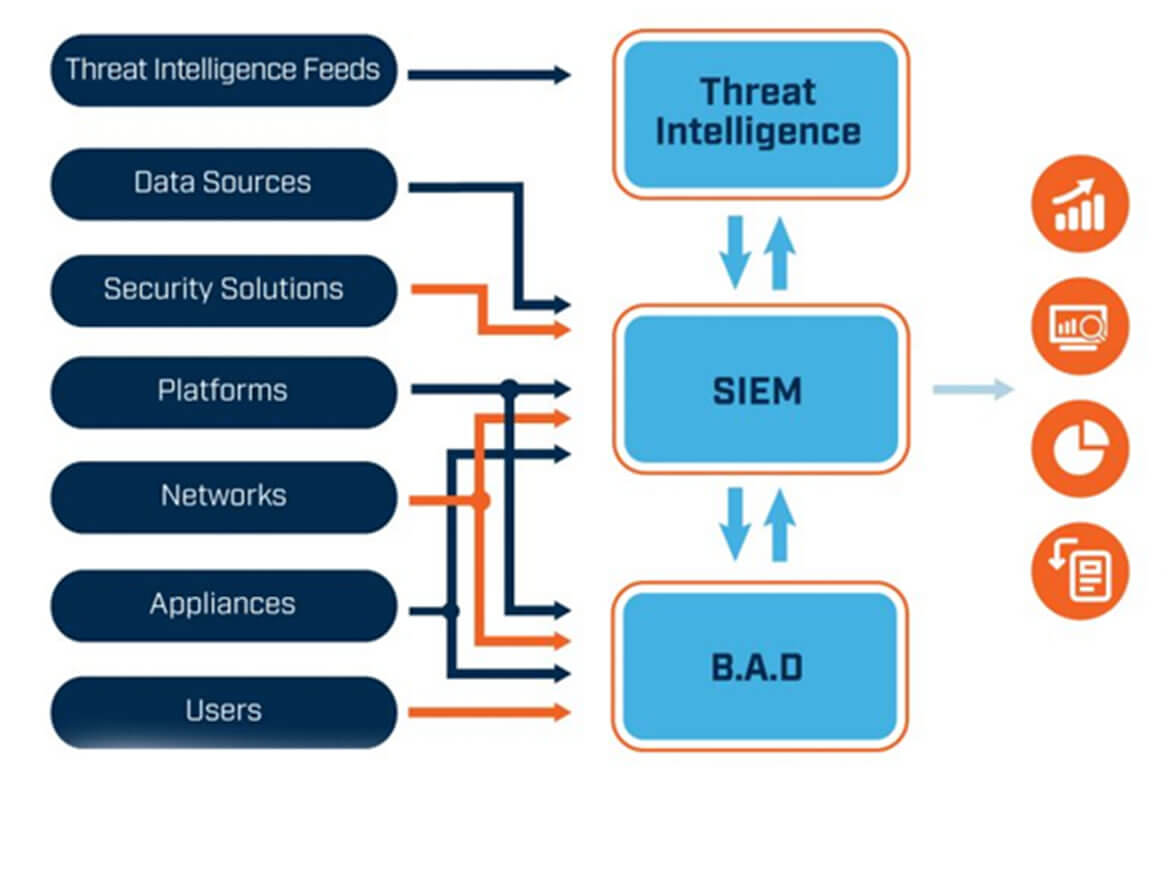
Next Generation SIEM & Security Analytics
This disparity across systems and applications makes the job of a forensic investigator complex and time consuming, which is why Security Information and Event Management (SIEM) systems were originally created to offer organisations a way to pull together these events from across the enterprise and store them in a standard format in one location.
Protect audit information
By using a SIEM to collate your digital evidence you can use it in investigations and potentially even court cases, should an investigation lead to a prosecution. A court will consider the ‘evidential weight’ of your records, which refers to the value the court places in the evidence presented, and whether under analysis from an opposing attorney it could be discredited.
It’s very important that in designing your audit and accountability solution you consider the need for protecting the logs in a way that ensures they cannot be tampered with or deleted, since their integrity will be a crucial aspect of the investigation and presentation of the case to the court.
Most SIEM platforms store logs in a forensically sound manner, where digital signatures and timestamps associated with receipt of the original records are also stored in the database. Nevertheless, log sources are where attacks tend to happen, since attackers are savvy to the concept of logging and will endeavour to destroy any evidence associated with their malicious activity.
System administrators should be encouraged (by their security counterparts) to ensure logging solutions are protected and attempts to stop, flush or modify the audit collection is immediately alerted to the security team for investigation.
As events traverse the network to the SIEM, there will be opportunities for interception and potential modification. To ensure that integrity cannot be refuted in court, encryption and digital integrity measures should be used to protect all log information in transit.
Finally, access to the SIEM should be tightly controlled, with only the most trusted security investigators having access to the full dataset. Analysts working in a Security Operations Centre (SOC) should never need to access the SIEM’s underlying database, so make sure the actions SOC analysts can take are constrained to their job role.
CMMC and Next Generation SIEM
SIEM solutions have evolved into modern, fully featured security management tools supporting governance, risk and compliance, as well as a raft of operational support capabilities such as threat detection, verification and alerting so that security teams can quickly detect and isolate attacks before they cause harm. The fundamental capability of SIEM to aggregate logs in a forensically sound manner is an important element of security management to guarantee the irrefutable audit and accountability required by the CMMC.
 About Huntsman
About Huntsman