Growing, mid-size companies that want to avoid or survive cyber crime face a tricky challenge as they are often overlooked.
There is a great deal written about security for SMEs – advice for companies that have very limited resources and are small enough to just need the basics. There is also a great deal of thought put into how large enterprises should handle security, with structured teams, technology stacks, operational processes, certifications to standards, organised departments, growing budgets and incumbent service providers.
Often advice to mid-sized companies on cyber security risks (if it exists at all) is driven by a rather lazy categorisation of them being “in the middle”:
- Not big
So they won’t have well-resourced, multi-disciplined, structured teams and infrastructure.
- Not small
So with “greater than zero” IT budgets/resources.
In effect, in an “inverse Goldilocks” zone:
- Cyber security for Large Enterprises
This is well covered as there are bigger risks, bigger budgets, more scope for solutions and services and mainstream media headlines when there are failures.
- Cyber security for SMEs
A very popular Internet search, white paper and blog topic (we’ve blogged on this specifically here). There are many sources aiming to help this segment of the market such as the NCSC guidelines (NCSC Small Business Guide) and the GCA SMB Toolkit (which can be found here).
- Cyber security for mid-sized companies
They are too big/complex/significant to be fly under the radar and follow the generic advice given to SMEs but not big or well-defended in the way a robust and resourced large enterprise is (or ought to be).
Their cyber security porridge is not too hot or too cold. It is both.

Cyber security needs to be “just right”
However, you can’t formulate a strategy based on the problems, resources, constraints and requirements you don’t have.
It needs a bit more thought than that. The “size” factor isn’t as helpful for these reasons, instead it is better to consider the approach to cyber security based on the “stage of development” a company is at.
Cyber security: Stages of company development
There is a great deal of research on how company development progresses. As businesses grow and change there are differences in approach to many aspects of how they operate in each phase:
- The small/start-up phase is where the business is focussed on early sales, on market awareness, on gaining reference customers or a track record, on cashflow and typically has a single person fulfilling each role within the business (or single people fulfilling multiple roles).
- The next phase means increased size and a business that is seeking wider market penetration and exploring new markets, customers, territories, products. A stage where there are multiple people, or whole teams, working on common tasks.
As a simple example – a new business owner will do all his/her own sales, as the business grows there might be a dedicated sales person employed. Then by the time the company has reached a mid-size point (whatever that means) there will be a sales manager and below them a set of sales people with different focuses working as a department.
Many aspects of this development process, including cyber security, can be likened to the process of raising children (and this is reflected in the advice given to businesses of different sizes).
There is a sequence you go through with kids… You start out by doing everything for them, then you help them do things, then they do things themselves but with you watching, then you give them a bit more independence and maybe check things have been done (“Have you brushed your teeth?”), and finally they become largely able to look after themselves (in theory).
In short, you have to learn to delegate. Cyber security is no different, however, the effectiveness of your cyber security strategies must remain visible; this is where reporting becomes critical.
As companies grow, cyber security evolves from being a small, side task that the owner/manager does, to something that is done by an embryonic IT team, to a role for a person who oversees the delivery of security, then a small team or growing department that is focussed on it.
The technical approach and the way controls are implemented, operated and overseen follows hand-in-hand with this as the business itself changes.
So, the “right” approach to cyber security is one that matches the delivery of cyber security in a way that is appropriate to the “stage of development” of the business, rather than being based on the “size” that it happens to be at the time.
There are lots of studies on company growth patterns. Including this one in the Harvard Business Review.
Cyber security for growing companies: Risks and Impacts
One of the most obvious differences that growing, mid-size companies must consider is the risk they face, primarily in terms of the scale of impact. At these stages of growth companies can ill-afford major losses.
A smaller organisation is more focussed on cashflow, profitability and sales; but as the company grows it has more intrinsic value (including to investors) – but won’t yet be big, or mature, enough to absorb large expenses or deal with complex events like a major cyber crime attack.
When companies are young and small the effects of major failure are felt by only a few people and, in cyber security terms, will often matter less compared to other business issues (like cashflow, sales, market awareness).
However, when a business has grown, matured and has more structure; with departments of people filling similar roles with a common focus; then there are suddenly more business risks that can affect the wider range of products, services and customers. Not to mention the fact that more peoples’ personal data, employees’ livelihoods and supporting businesses can be affected if a major upset occurs – such as a high-impact security breach.
As a business develops, the numbers of customers – either B2C or B2B – will be larger and so the impact of a stolen customer database or breach of intellectual property is higher as well.
A large, more established business might have multiple service lines or products across which costs, profits, risks can be managed. However, a younger company is likely to have a much narrower focus around a single/limited product family or service area because it won’t have had the chance to diversify.
For many businesses at this stage of growth the technology decisions, understanding of risks and management of incidents are activities are being done for the first time. So, it is not so much that a big company is better at managing cyber crime risks than a mid-sized one; they have just had more experience of doing it at the stage of maturity they have reached from having had past incidents to learn from.
Ownership is also a factor, a very small business might have a sole, or small numbers of owner/managers. Large enterprises are often listed on markets and hence regulated. In the middle ground there are likely to be owners or investors who are not directly involved in decision making – including about cyber risks. Hence there is a need to focus risk management decision making on a broader ownership group, one that expects sound decisions but isn’t party to making them.
Growing companies won’t have developed the structures that a larger, listed company would be forced to have. They won’t have evolved a culture where risks and compliance go hand-in-hand the way they it should when corporate governance has become more established. Once again, it is more useful to consider this as a factor of “stage of growth” rather than “size”.
In all these cases and examples, the two elements that are important to accelerate are the maturity of how the business defends itself against cyber crime and the visibility it has over the risks; even a small company can respond quickly to a major risk if it is made aware of it.
Maturity: Delivering outcomes with managed services
The result of this is an environment where risk understanding and decision making must be sound, visible, transparent and defensible in their own right. In many respects this is exactly why companies that are growing often commission managed security service providers (MSSPs).
MSSPs allow the leapfrogging of several stages of cyber security maturity by giving businesses access to a third-party provider that has built the maturity, technology stack and processes as part of their core business service offering.
MSSPs provide a range of services from configuration, operation, administration, monitoring and incident response. But importantly, they deliver an “outcome” to a business that hasn’t had time to grow the people, processes and technology to evolve its own technical delivery capability to achieve that same result.
Sometimes as mid-sized organisations become much larger they bring security operations back in-house. This isn’t a criticism of the way MSSPs operate or their value, just a reflection of the evolutionary stage of maturity and capability the business has reached.
Visibility: Better understanding through KPIs
One of the first things a business has to do as it grows is establish sets of objectives and KPIs around functions to enable those in senior positions to see how they are performing, as the expansion means they have less direct involvement as management structures expand.
Cyber security is no exception, but it is a function that aims to stop things happening rather than to make them happen. It also often sits within an IT function that will be about providing services (making things happen) at the lowest cost. It can be a challenge.
If you stop a cyber crime you have nothing to report (despite being obviously successful); in fact, you have nothing to report until you fail.
Likewise, if you weren’t previously looking for signs of attack, and then you do start looking, this increased cyber security vigilance results in the number of attacks being reported also increasing (which can appear to be a bleaker picture than before – you spend more on security and get more alerts not less).
One way to address this, in a way that scales well from earlier stage companies right up to the larger enterprise space is to track specific, measurable, risk-based controls and metrics. In short, to define a set of key risks and then highlight the controls and operations that mitigate them.
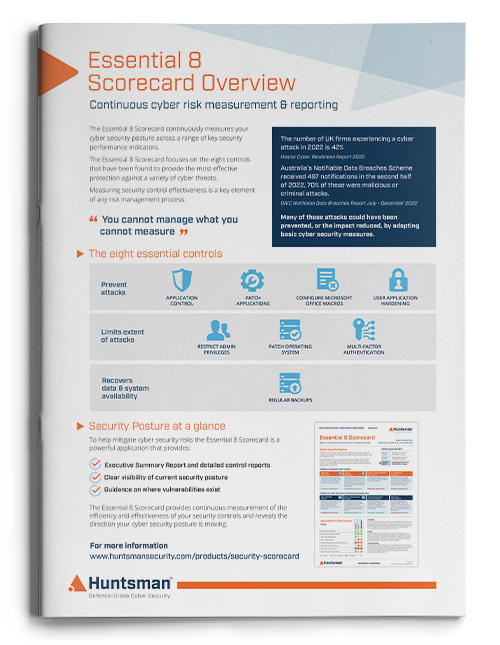
In this way a “balanced scorecard” of detective, preventative, operational and responsive control effectiveness measures can be derived. These should be as simple as possible – operating system patches, correct configuration of admin accounts, successful backups etc. – where the target and actual KPI can be defined and measured in an easily automated way.
A good example of this is the Australian Government’s Essential 8model. This covers 8 key controls that between them have been found to mitigate 85% of cyber crime threats; hence if they can be measured it gives a good view of the specific levels of defence, but also the overall posture a business has in countering cyber crime threats.
Scorecards, especially if they are live, automated and machine generated, benefit from low cost of operation, freedom from human intervention and bias and provision of clear visibility of the levels of risk faced. These same attributes are what makes them easily scalable and suitable for businesses as they grow:
Inexpensive to set up and deploy, yet clear enough to give growing management structures effective visibility.
 About Huntsman
About Huntsman