No company wants to be the target of cyber criminals. Attempts to steal data, IP and personal information, encrypt data to get money or create botnets for mounting other forms of attack are increasing all the time. The cyber security challenges that companies encounter continues to grow in the face of an increasingly organised and hostile Internet-based criminal fraternity.
Staying free of cyber crime
There are however some fundamental things to get right if your business wants to stay crime free. They are the online equivalents to closing windows and locking doors as a defence against real-world crime – and they can really help.
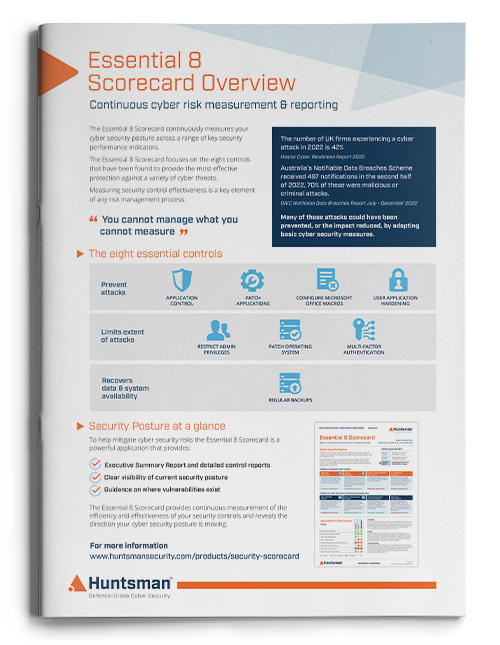
The recommendations below are based on Australian Government findings that 85% of breaches were either caused, or made worse, by ineffective controls in 8 areas.
The list is not intended to be complete and there are other obvious controls that are important too – like staff awareness training or having anti-virus software installed. However they found that when those types of controls failed, it was this list that was most useful to try and avert an attack or minimise its effects. So when antivirus software fails to pick up a brand new virus, there are steps beyond it that become part of the essential line of defence.
Patching Operating Systems
Operating system vulnerabilities are common, and to a cyber criminal they represent an open window. They are easily detectable and a simple way to access a system and the data, user credentials and files it contains.
The diversity of systems and the challenge of knowing whether business applications will still operate on the latest patched OS versions, coupled with the need to plan in downtime for servers, does make patching more complicated. The frequency of updates and their deployment is a challenge for large and small environments. However, this is an area that simply must get focus if companies want to avoid being a victim of cyber crime.
For many businesses there is a lack of knowledge as to exactly how well the process of patching vulnerabilities operates. Understanding where residual exposures are is therefore a key report to have at one’s disposal.
Patching Applications
As with operating systems, the applications we use can contain vulnerabilities too. Once again these can be like a known open window to cyber criminals.
In the same way an operating system can be exposed and used to access systems and data files, data sent to applications can achieve the same end and it is applications that we use to open documents, PDF files, emails and spreadsheets.
The complexity here is greater, as for every system that has one operating system on there might be dozens of applications all from different vendors; and users might even install their own.
Hence the problem is magnified and the importance of making sure the latest versions/most up to date patches are installed is just as great.
Managing privileged users
There are two aspects to this.
One is that users with administrative accounts have enormous ability to do wrong if they become disillusioned or dishonest or compromised in some way. So it is important to make sure that people only get the access they need to do their jobs. If that is a highly privileged account then there has to be a process to validate that they need it (and that when they no longer do, it’s removed) and a way of monitoring their use.
The second aspect to this is that there should be controls around what admin users can do – in view of the threats they pose when using those accounts. For example, allowing admin users to access email and or browse the internet is risky as a stray link, a drive-by download or other piece of malware can gain an enormous foothold if it is triggered by someone with the keys to the kingdom.
Administrative users have the power to allow or grant themselves these kinds of conveniences or abilities, even if policy forbids it and so preventing and monitoring these configurations and settings is important.
As such it is not just the administrative process of granting/revoking the high level accounts, its controlling and monitoring what is done under them when they are used.
Controlling use of software
These days there is an application for almost everything.
Give a person with sufficient grasp of computers and the Internet a problem, and a few searches later they will have found a software solution and be in the process of installing it.
The challenge for IT and security teams is two-fold, one is the plethora of applications and software they have to accommodate and manage, the security issues and patches, or the range of data types and silos of information.
Then there is the perennial risk that these solutions actually introduce processes or data flows that themselves are security challenges.
For example, a cloud-based contact management solution that allows the business user to track and share contact information; but which also (from the security point of view) exposes potentially sensitive data to a third party based who knows where. Software download and installation records, as well as the results of asset or software inventory processes are key in detecting these types of threats – or at least flagging them.
Hardening applications
Where authorised or standard applications are used it is important that they are configured to provide a degree of security protection. This is particularly relevant for web browsers as they are a major touch-point between the user’s systems and the content pushed out on the Internet, including that put there by cyber criminals who have malicious intent.
The battle against drive-by downloads, malicious web code, and other harmful content can be partly fought within the browser configurations used (irrespective of which browser). A good place to start is with the types of content that can be executed as code – whether it be JavaScript, Java or other forms of client-side executables.
The way in which sites or content or files are trusted, and the latitude users have to ignore security warnings, bypass requirements for security checks or download material, all determine the chances of someone in your organisation ending up as a “patient zero” for some form of malware or browser based attack.
Blocking macros
Macros are still a common way for malware to spread. The ubiquity of Word and Excel and their rich programming languages means that these applications and documents containing macro code can introduce significant risks.
If enabled, macros can be invoked by downloaded or received documents and there is a clear threat of a malicious criminal actor being able to get their code running in your environment by virtue of a user opening a file that they believe to be harmless.
Backups
Backups are a key part of business resilience, and where hardware fails or data is corrupted they have been known for some time as being indispensable.
In the world of cyber crime and ransomware though they also are critical to being in a position to avoid paying a ransom (and hence funding further crime) and avoiding data loss when systems and files are maliciously encrypted.
Some “ransomware” is actually faulty and data decryption might not be possible, or it might – as in the case of NotPetya – be designed to look like ransomware but actually not allow decryption at all, so backups are the only true way to avoid data loss.
The importance of backups on both servers for critical files (which should already be in place), and also at the workstation level (which is much less likely to be comprehensive) has never been as great – making sure that the schedules are running and that failures are resolved so data sets are timely and complete is essential.
Multifactor authentication
Multi-factor authentication (MFA) is a good idea but can be intrusive. How and where you use this technology is therefore often a local risk decision – but for web site/app-based customers and highly privileged users it is a powerful way to avoid the inherent weaknesses of passwords that are often poorly chosen, used across multiple systems or written down.
If a user’s keyboard is being sniffed or their password file is exposed, or if the web site backend data containing the user credentials is stolen; multi-factor controls might be a saving grace. Preventing access to accounts by attackers and criminals, even if they do know the passwords to get past the initial login prompt, is becoming much more widely expected for sensitive data and high level access.
Cyber Crime: Winning the fight
As we said at the outset, the recommendations above are not exhaustive. There are many other security controls needed to provide a robust defence and keep a network crime free. However the safeguards and processes listed here, based as they are on practical experience of past breaches, are the most essential ones to have in place and working effectively. They account for the commonest attacks and those attempts by cyber criminals to subvert specific controls like anti-virus gateways or proxies.
The level of maturity in these areas, if it can be monitored and tracked over time, is a fair bellwether for the overall cyber resilience and risk posture of the business and the best way for the board to understand the cyber crime risks it faces.
If you have got these controls in place and working effectively, you will be much safer than if they are ineffective or not in place at all. If you don’t know how well your business is performing in these areas, then it is important to find out.
 About Huntsman
About Huntsman