For people who have been working in security for some time there has been an evolution in communicating cyber crime risks to the board; this has gone through several phases from initial disinterest, through necessary but begrudging acceptance to a point where now measurement of the state of key risk indicators is actively sought.
The evolution of cyber crime risk reporting
Back when we called it “Information Security”, it was often perceived as a business barrier and so the desire to get it on the board agenda to explain the growing importance of information, and the risks to it in terms of confidentiality, integrity and availability, was often met with a distinct lack of enthusiasm.
Then we called it “IT security”, and it became the domain of the IT department and sat alongside availability and functionality. “How quickly could the business get a new transactional web site on-line” was seen as more important so they could start selling goods and services.
Security teams wanted to highlight that systems were vulnerable to viruses and hackers (and worse, “script kiddies”) but these warnings often came late in projects or appeared to hinder progress. There was so much resource and effort devoted to IT and an ever-growing technology budget, yet so little focus (and budget) on security – it just wasn’t an “enabler”.
Cyber security … Ch-Ch-Ch-Changes
The widespread reports of security breaches and successful data exfiltration hastened the advent of the term “Cyber Security”, which truly changed board level perception of security. This, and the emergence of a cyber security insurance and underwriting industry, began to highlight the risks and related costs associated with targeted attacks, compromise of personal information and the increasing problem of IP theft by organised crime as well as nation states.
Cyber security became acknowledged as something that could affect the well-being of the company, its profitability, its customers’ personal data, the business “information crown jewels” and, for the directors, it became a fiduciary risk that could ultimately affect their roles as business leaders.
Put simply, it changed to become a risk they were responsible for and needed to have visibility and management of. “IT security” wasn’t renamed “cyber security” it was translated, re-branded and monetised.
Boardroom understanding of cyber security
There is always a challenge in explaining technical subjects to non-experts but often, and in this case, it is vital. Explaining cyber security risk means finding a common language, a way of translating a security risk into the recognised business lexicon of risk and its measurement. What is the potential impact and equally important, in order that it can be prioritised, what is its likelihood?
In cyber security we are faced with a deliberate and motivated adversary targeting our assets. In other areas of risk management we are dealing with accidents or non-deliberate events. We have, over time, developed tools and techniques to mitigate all but the most malicious threats.
In risk management terms, markets may move against you, exchange rates could shift and hurt your profitability, data centres could flood or there could even be environmental issues – but for many of these we have developed thresholds and indicators to determine or statistically predict them as real-world events.
How do you determine and quantify the risk in an ever-changing cyber world when the source of a threat is more deliberate and often more targeted?
Prioritising cyber crime initiatives: Prevention, Detection, Response
Today’s reality is that you won’t achieve a perfect record by defence alone. The maxim that it is “when, not if” you fall victim to cyber crime is now widely accepted as holding true.

Its important to try and stop cyber attacks, but you might not be successful
Consequently investment, effort and attention must be on more than just prevention, but also the continuous state of your defences. You need the ability to “notice” when a cyber crime attack occurs or when there are indicators of compromise present and the ability to react effectively.
The reasons this is important are three fold:
- The longer an attack is in progress the more damaging, expensive and embarrassing it is.
- The records of activity that will help you diagnose what happened may be transient and might only be retained for a short time; and if you are trying to diagnose, understand and deal with a breach from some time ago evidence can be hard to find.
- If you don’t notice a breach yourself then it’s likely that someone else will. Customers may spot fraud, the press may get wind that you’ve fallen victim to a cyber criminal, a regulator or external body might notify you. It can be deeply embarrassing – not only did you get burgled, you didn’t even notice.
Technical information and Business risks
One of the biggest failings in the way cyber security risks are conveyed to the board is the use of technology heavy terms, figures and metrics.
A list of 50 vulnerabilities or security issues that are being worked on does not give any indication of the financial or business risk value. 500 problems in a population of 10,000 workstations might not sound too significant. However, a single critical unpatched vulnerability on a sensitive server, could be hugely damaging.
You need to have a way of measuring the business risk associated with your cyber posture at any one point in time. Risk based decision-making is a key development in prioritising what is important for boards and what is not when it comes to cyber security.

Cyber risk decisions need to consider many factors
Exposure to cyber crime via third parties
Just when you start to think you have a satisfactory risk based cyber security process in place for your information systems, you realise there is a far wider scope to the problem of cyber crime. What about the scale and scope of risks posed to your business by third parties, and the exposure of your data to their unprotected systems; significant new exposure to cyber crime can be introduced. You are only as robust as the weakest link in the supply chain.

Cyber crimes can happen anywhere
Measuring and managing these risks is an added responsibility that often means a complex programme of audits, self-assessments, sample-based scanning of systems and contractual safeguards – interfacing not just with IT but with businesses , procurement and commercial teams that handle the terms and conditions, and auditors who oversee the arrangements.
It is a lot of effort and money, particularly when your systems regularly interface with much smaller enterprises and other organisations that might have an under-resourced or divergent cyber risk management approach or risk profile. You can be left with a high degree of uncertainty as to your exposure.
First Question – What security controls do you have in place?
What the board needs to know is “What are our key assets and systems and how safe are they?”.
This means high-level, business-based risk information that requires effective key performance indicators and their ongoing measurement.
Start by looking at the security risk mitigation controls you have in place. If you are not sure where to start, look at recommendations from government bodies.
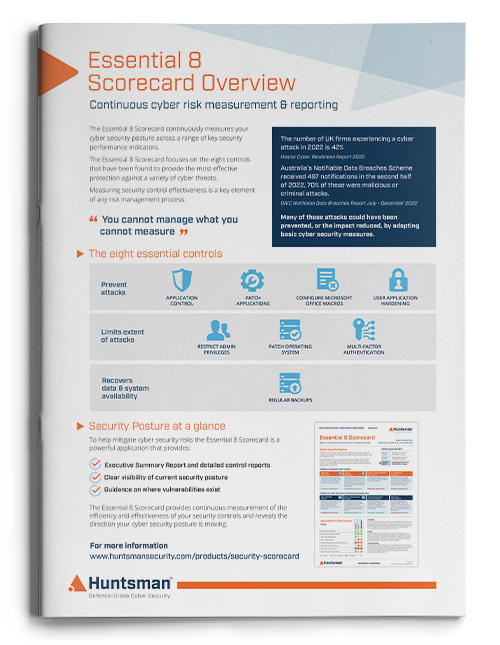
The Australian government has found that just eight key security controls can help protect an organisation against up to 85% of targeted cyber attacks. You can read more on this here.
Similarly, in the UK the National Cyber Security Centre has published a “10 Steps to Cyber Security” guide that covers the primary areas they view as important in delivering an effective security posture. We have produced a handy guide to this here:
 The Essential Guide to Cyber Security – Following the NCSC 10 Steps to Cyber Security
The Essential Guide to Cyber Security – Following the NCSC 10 Steps to Cyber Security
Second Question – How effective are your security controls?
Irrespective of what and how many controls you have in place, they will only be fit for purpose if they are implemented properly, operating effectively and are meaningful.
Monitoring security controls for effectiveness is paramount to managing your organisation’s cyber resilience.
Key Performance Indicators (KPIs) are well known in all areas of business as they present a quick and clear assessment of performance and situational awareness across an acknowledged set of key business-focussed measures.
Developing cyber security KPIs for your business means that your security team will have an effective and current (and comparative) view of your security status. Additionally, the information can be reported simply and concisely to all stakeholders in the business: auditors, risk managers and the board.
Cyber Security KPI Reporting
Finding an objective and continuous way of reporting your cyber KPIs has been a challenge for security teams over the years. However, advances in security analytics tools, dashboards and Security Scorecards now mean that your security team can measure your posture and quickly take positive action against a list of prioritised threats rather than wading through a never-ending avalanche of unprioritised, semi-interesting, and irrelevant technical data.
KPIs like this can also be used by the security team to show improvement in operational performance or to seek budget for additional technology or resources.
Using business-focussed, quantitative metrics to derive reportable KPIs in cyber security must be a good strategy; it is the way the rest of the business reports and manages its progress after all.
 About Huntsman
About Huntsman



 The Essential Guide to Cyber Security – Following the NCSC 10 Steps to Cyber Security
The Essential Guide to Cyber Security – Following the NCSC 10 Steps to Cyber Security