After all the coverage that cyber crime gets, there is often still much uncertainty in the minds of business stakeholders around what the risk is, what could your exposure to it be? What does the impact look like if you are affected?
Cyber Crime: Who feels the impact?
When considering the impacts of a security breach, data theft or cyber attack it is worth considering “who” the impact is actually felt by. The impact on an individual, or a company, or a manager in that company can be very different for the same breach situation.
The entities that suffer from a cyber crime are very different; it is almost the opposite of a “victim-less crime” in a sense, as potentially everyone involved suffers, not just the direct victim:
The Organisation or Company
The organisation itself is often the victim (in the most direct sense) of cyber crime as the data it holds is accessed, stolen, corrupted or used to embarrass it or damage its operations, profitability or reputation in some way.
Customers, clients, service consumers
The people that the organisation sells to, services or deals with – the “general public”. This could be a large number of people (as in recent high profile data breaches) or a single individual who has a file, record or document accessed.
Third parties
Other organisations with whom the main target has a business relationship can also be affected by cyber crime. They may or may not be implicated in the breach, they could just be impacted by it.
As a simple example the Target hack was made possible because a HVAC contractor was initially breached and held access credentials to the Target network. In one sense the contractor was the initial breach site, Target was just an unlucky customer of theirs who had their “sensitive” information stolen.
However, after the fact, it is the breach that affected Target that everyone remembers.
Shareholders
Shareholders suffer in an odd way. Often when there is a serious breach the share price drops in response. However, over the long term it is unlikely to stay too depressed as a breach doesn’t often shake the company’s underlying ‘fundamentals’ (although in some cases it has).
For example, very few people would have been put off buying a Playstation 4 because Sony suffered an attack back in 2011; the console capabilities, selection of games, brand and PlayStation network/store eco-system are a big enough draw for that generation of video gamers to overlook a past data breach.
As such shareholders might suffer a short-term impact and worry that revenue and profit is being tied up in rectification, but over time this evens out. In fact a shareholder would be equally worried about a company spending too much on security provisions and “over protecting itself” (thus impacting profitability) as it would suffering a breach.
$4m spent on controls that aren’t necessary (or effective) is a guaranteed loss, definitely affecting the bottom line. Saving this money (by not investing in controls) only becomes a problem if the company suffers a resultant security breach that it has to address. If it is lucky instead, then that $4m becomes profits and dividends.
Individual Managers
Most modern businesses have structures in place now to avoid falling victim to the whims of individual managers. An IT manager seldom has carte blanche to go off and spend a large sum of money on a solution without recourse to their manager and procurement/commercial functions.
This does mean that when things go wrong, when cyber crime occurs, there is seldom only one individual responsible; so the impact on a particular manager might be limited if they didn’t have the budget to adequately defend systems, or weren’t allowed to deploy technology or add headcount for which they had asked.
However, there are cases where senior-level decision makers; those with oversight responsibility for areas of operations; have been forced (or chosen) to leave their positions following a breach. After the Equifax hack the CSO and CIO left (or retired), followed by the CEO as well.
Cyber Crime: What is the “Impact”?
You should also be aware of the types of impacts that may be suffered. There are lots of potential impacts, but often they boil down to a small number of “end results” or “eventual impacts”.
Financial and reputation
A company or “responsible manager” may suffer a financial or reputational hit from cyber crime. These are often interchangeable when you consider the implications of a reputation impact. The financial loss might be from paying for the investigation, paying lawyers, paying regulatory fines, paying compensation etc. (i.e. the “cost of the breach”).
Where the reputation is affected this again has a bottom line impact – either increased marketing and sales spend to attract new customers despite the breach, having to lower prices to be more competitive, having to offer better deals to existing customers, having to – in short – pay more to gain/build/earn trust and compete again.
The individual manager or “person responsible” (the person whose job it was to avert, prevent etc.) may suffer a job loss, or impaired career – but losing your job or having your professional reputation mired has a financial end result too.
A terminal event
In extreme cases – a massive loss, a serious regulatory breach or a loss of critical Intellectual Property (IP) – could, of course, mean more serious impacts for an organisation.
If the financial impacts, costs, reimbursements, restitutions are of such a scale that the financial health of the company or organisation is impacted beyond the point where it can recover then clearly the end is nigh.
Similarly, if its reputation is impaired to the extent that the loss of customers, or the ability to attract new business cannot be turned around, the same outcome can happen (again, the reputation damage translates into a financial impact).
Clearly, when a business closes its doors the implications spread way beyond those responsible for the breach. A bankruptcy or cessation of trading will impact every single employee and also might have a knock on impact on businesses that trade with that affected organisation (i.e. suppliers who lose a customer or customers who lose a supplier).
Inconvenience/Embarrassment
Some security breaches and cyber crimes go beyond financial impacts or reputations because of the nature of the information disclosed. A good example might be medical records information that of course pertain to individuals and are fixed; so if you had an embarrassing disease at some point – that fact, once revealed/public, is revealed for good.
Similarly biometric data, if exposed, cannot be reissued, reset or revoked – it just has to be accepted as compromised. It may be flagged as unusable, but it is still forever lost.
Good examples of this would be the US breaches at OPM (Office of Personnel Management) that contained clearance and personal history information; and Ashley Madison that contained details of people who were looking to have affairs. Information that once disclosed could not be “undisclosed”.
What motivates the attackers?
The nature of an exposure may well be linked to the motivation of the attacker in any given case of cyber crime. A financially motivated criminal is most likely to cause financial loss – but it might be the impact on your reputation that causes the most distress, upset and financial penalty.
So an attacker may seek to defraud you or your customers. Clearly the financial costs will rest somewhere; and the clean up, recovery, reimbursement charges fall alongside the investigation and fines.
An attack might be motivated by a desire to embarrass an organisation or harm its reputation; even point out how lax its security is. This often involves publication of stolen data (sometimes partially obscured or obfuscated) and details of vulnerabilities.
Here, the damage is often less financial (although there may still be fines and compensation to pay) but chiefly the embarrassment and any potential impacts to customer numbers, the wider strategy or operation of the business is the chief outcome.
This class of motivation also includes hactivism; where the embarrassment is driven by an agenda, ethical or political motive. Government, law enforcement, large corporates all find themselves the victims of these types of attack where the aim is to “get one back” for a real or perceived slight or an unpopular decision that has been made.
However, the most damaging impact, and hence the most worrying attacker motivation, is when the goal is the information itself; I.e. an attempt to quietly access information – either sensitive personal records or critical organisation IP for the attackers own use.
Here there is no big unveiling, no publicity backlash, no huge embarrassment – just someone who uses the stolen information to steal customers, understand your pricing, develop alternative solutions and to subvert your business success to bolster their own. Several, state-sponsor examples of this exist.
Cyber crime – Remaining questions?
The largest challenge then, having understood the nature, extent and type of threat, is to ascertain the likelihood of a cyber crime being perpetrated “on your watch”.
Bad or worse
First assess the realistic scenarios (some of which are described above) for cyber crime that might affect you.
If you are a small medical or financial advisory business with a large number of customers and you suffer a privacy breach, then the fines and pay-outs might be more than you can stand simply because of the numbers involved and the need/cost to restore trust.
Conversely, if you are a large plumbing firm but only hold names and addresses maybe the impact is lower as the sensitivity of the fact that I once had a leaking tap is much less, and so probably I’ll just use the same trusted supplier again when my toilet won’t flush.
If a software company, or manufacturer of a uniquely designed product lost their IP they may find they can’t sell their product any longer due to a large number of duplicate products flooding the market.
So consider how “realistically bad” a breach could be. It will be “bad” but it might also be much, much “worse”.
Likely or unlikely
Is it likely that you’ll be a target of cyber crime? Does your business have a large volume of valuable customers? Is your unique IP well known as being ground-breaking?
Are you working in an industry that is contentious and hence could be the target of activists (animal testing, environmental issues, the political sphere, defence etc.)?
Are there people out there that would crave the data you hold, or members of staff that would feel disenfranchised enough to either steal it or leak it?
Basically: “Are you a target?”
In theory everyone is a target, and if your security is weak (see below) you might be a target not because your business is controversial or valuable, just because you are an easy target; and hence get attacked by someone “because they can” or because they feel they have a duty to expose your failings.
Easy or hard
Finally it is worth being honest about your organisation’s cyber posture; how difficult it would be for an attacker to gain access to your networks and systems, how easily an employee (if they were so minded) could steal data, or how likely it is that a member of staff would click on a suspicious email link and infect the network with malware inadvertently.
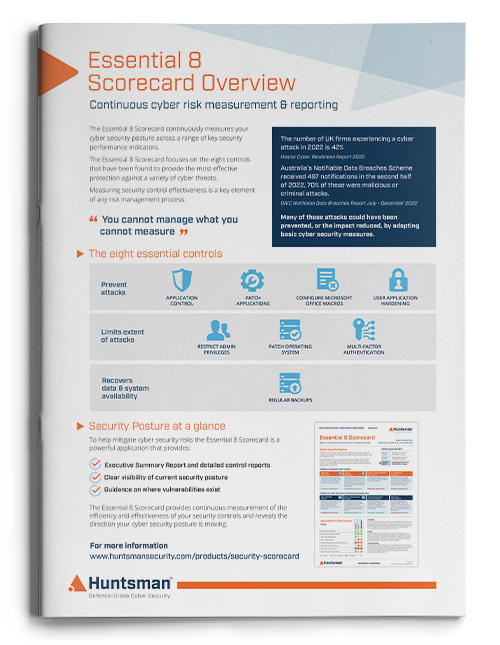
This comes down to having controls in place, having sound processes in place to manage, operate and monitor those controls. It also means being able to say that the effectiveness of that control environment at any point in time is trustworthy and assured.
You have a firewall but is it configured properly? You have data in the cloud but how easy is it to access? Your staff have email but do they click on links and open attachments or try and check the origin? You have IT systems but how up to date are they; how often are they patched?
The answers to these questions are important – and you should know them not just at a “point in time”; but on a continual and ongoing basis because these are areas where a failure can have a very direct business impact on something the management cares about: brand, reputation, or bottom line.
 About Huntsman
About Huntsman