Whether as a result of increased governance at Board level or simply improved performance management practice, cyber risk measurement and management is now acknowledged as an important 360-degree risk mitigation strategy to support your corporate risk management responsibilities.
Cyber risk rating and reporting
To address the existential cyber risks your organisation faces you need to improve the quality, reliability and accessibility of your cyber reporting.
The interdependency of IT systems highlights the increasing need for organisations to better understand the state of their security defences; and those of their partners. Published cyber risk ratings or a cyber security score can benefit of all stakeholders – investors, shareholders, partners and commercial counterparties – by providing a relative measure of the state of cyber posture for the organisation.
A poor cyber score alerts us to a vulnerability within an organisation, which could result in major commercial costs for all connected parties. It is increasingly important to know the cyber risk status of those you deal with. Look no further than the widespread supply chain issues caused by Spanish online survey company Typeform’s data breach back in June 2018.
Effective cyber risk measurement communicates important risk information that is clear, simple and timely for management and decision making purposes for both cyber security and management stakeholders.
Cyber risk management due diligence
The ability to measure a common set of key cyber performance indicators (KPIs) enables organisations to undertake appropriate due diligence and supports security staff in the pre-emptive mitigation of any identified risks; improving the overall cyber posture of their eco-system or supply chain in the process.
A recent Gartner report has gone so far as to suggest that by 2022 “a trust index” or security ratings will be as important as credit ratings in the risk assessment of existing or new business relationships. See “Innovation Insight for Security Rating Services”, a report published on July 27, 2018 by Gartner.
Cyber security scorecard ratings
There are a number of cyber security scorecard solutions available in the market that provide an assessment of an organisation’s security posture or cyber risk rating.
As you would reasonably expect, the more objective and systematic the “measurement” process the more reliable the risk rating; the subjective nature of self-assessment and data sampling has been shown to be overly optimistic in its measurement of cyber posture (ANAO Essential Eight Compliance Report No 53, 2017-18, June 2018).
Reliability of the score – the importance of a recognised framework
A security scorecard should incorporate established, systematic methodology at its core, using a common language to communicate risk. Frameworks such as Australia’s ACSC Essential Eight, the UK’s NCSC Top 10 and United States’ NIST all provide comprehensive, tested strategies for mitigating risk and measurement.
How is the security rating of your organisation determined?
- A moment in time interpretation of external digital intelligence artefacts; or
- A systematic measurement of IT controls against a recognised, framework of KPIs
The essence of a sound security rating is that it is a verifiable measure that can be relied upon for performance management and informed decision making. Anything less is not fit for purpose.
Timeliness of the score – the importance of continuous measurement

The volatile nature of the cyber security landscape means that security ratings are far more dynamic than, for example, financial sector ratings; as a result, the security status of an organisation can change very quickly. Therefore, the more current and relevant the measurement the more accurate the cyber ratings.
Diagnostics and due diligence
There is little doubt qualitative metrics have value, the fact that a sensitive document was found on the dark web is certainly a cause for concern for any executive team. The next important step, however, is to determine the nature and extent of the potential risks that led to that event. Like every aspect of cyber security, attribution is vital, but when subjectivity and qualitative assessment become part of the scientific security management process, measurement based diagnostics are compromised.
Many organisations, because of concerns being raised by stakeholders, are turning to their own audit methods and quantitative techniques to accurately assess risk and report their cyber posture. These efforts bring reliability, confidence and currency to the measurement but are time-consuming, disruptive and extremely costly.
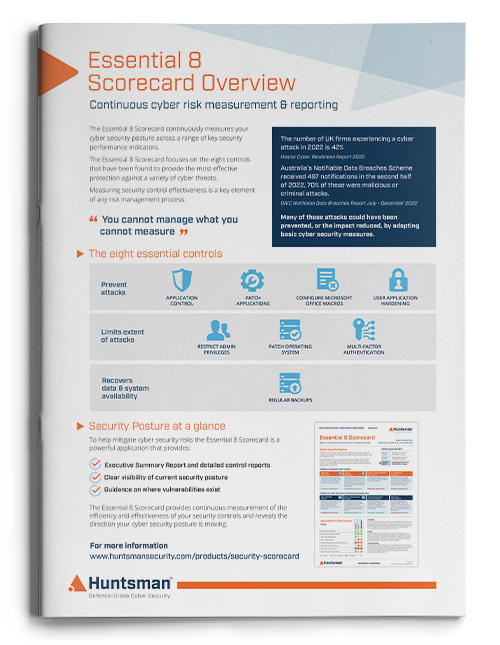
Introducing the Essential 8 Security Scorecard
Huntsman Security has developed its Essential 8 Security Scorecard to measure the state of defences and controls against the Australian government’s published ACSC Essential 8 framework; metrics are drawn from the systematic, ongoing monitoring of key cyber security controls.

The Essential 8 Security Scorecard delivers a number of important benefits:
- A continuous benchmark of cyber posture – enabling comparison between business units and partner eco-systems;
- Mathematically based diagnostics to quantify weaknesses in controls, pinpoint vulnerable assets and systematically calculate cyber risk ratings against each of the eight controls;
- Alignment to a reputable published framework with accurate, instructive and succinct measures of resilience;
- Automated, regular reporting, including the articulation of trend lines and lead indicators of cyber risks;
- Enables performance management of security posture – evidence-based, prioritised response to unsatisfactory cyber hygiene or non-compliance to the controls.
Qualitative and arbitrary risks assessments can certainly paint a picture but, without an empirical basis, they can easily compromise the decision making of risk managers and executives when responding to emerging risks. This can come at a very high price to organisations.
The Essential 8 Security Scorecard is a cyber risk management tool that simply and clearly informs on your growing corporate cyber security resilience for better business management outcomes.
 About Huntsman
About Huntsman