Outcome-Driven Metrics and Protection Level Agreements

Wherever you look, there are new and revolutionary applications of artificial intelligence (AI), behaviour analytics and machine learning starting to emerge. How can they help Information Security Teams?
As with many major new technology trends in recent years, the buzz has taken hold in the consumer space, with the likes of Apple’s Siri and Microsoft’s Cortana helping users to find information or access features on their devices based on speech recognition and certain predefined app or data access applications.
However, as technologies have advanced, businesses have realised that they have great potential in the corporate environment where automation and easier access to information resources also has a number of distinct applications.
For many organisations, the process by which they manage cyber security threats has been an onerous and manual one; reliant on scarce skills and individual capabilities.
Now, at a time when the level of cyber-risk has never been more acute and the reputational and regulatory impacts are increasing all the time, there are a whole host of organisations looking at ways they can harness these newer technologies with incredible capabilities to turn things around in the battle against cyber threats and organised, sophisticated cyber crime attacks.
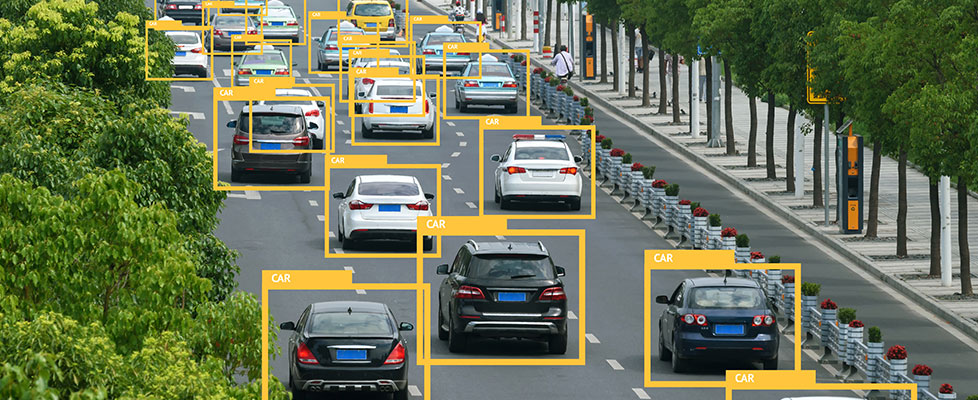
Security teams and technologies are now incorporating capabilities such as machine learning and automation to industrialise this previously manual process and help reduce operational risk by speeding up interactions, autonomously analysing data and providing clearly outputs and results rather than just a list of issues.
Security teams have been fighting an increasingly arduous battle as they tackle an endless barrage of potential threats and genuine attacks that monitoring systems and a growing raft of detective tools are alerting them to.
The problem is that the volume of these alerts has ballooned in recent years and there now just aren’t enough hours in the day or available resources to deal with the scale of the task. Each time an organisation invests in additional technologies to detect a greater breadth of threats it has to deal with the extra flagged alarms that are raised.
However, many of the alerts are likely to be false positives, minor or benign threats that don’t pose a significant risk (it is noteworthy that during proofs-of-concept or initial deployments it is in the salesman’s/vendor’s interest for the new solution to generate a high level of alerts).
Unfortunately, the volume and rate at which alerts come through once a new cyber security solution is “in production” means security teams suffer from information overload almost immediately.
Consequently, it is very difficult to deal with the levels of noise and to effectively prioritise or triage alerts to identify those that require immediate attention, those that can wait, and even those that can be disregarded entirely.
Unfortunately, it doesn’t look like this tension is going to ease any time soon. The number of devices on company networks is only set to increase and the deluge of threats and malware variants shows no sign of abating; especially as we see more financially motivated attackers, more diverse user endpoints and increased connections from IOT devices (Internet of Things).

All these factors are likely to add significantly to the burden on constrained security teams, by creating an expanding attack surface, with large numbers of potential entry points for increasingly sophisticated hackers to exploit.
It almost doesn’t matter whether the scale of the problem increases, or why this is. The growing threat, increased business scrutiny, continued shortage of skilled security resources – all these could be factors that drive this increasing challenge.
However even today it has become impossible for security teams to look at every alert themselves. We are already past the point of what a manual operation can handle unaided as the systems and processes for both cyber security defence and attack are already industrialised to a point beyond the realistic, scalability threshold of this legacy way of working. As time goes on, the challenge will only increase further as the cyber criminal, unbound by the limitations faced by businesses, outstrips the capabilities of the defenders.
Against this backdrop, there is a huge risk that breaches will go undetected for extended periods of time, resulting in severe consequences for enterprises.
There will be far greater impacts, more data losses, increased cases of fraud and more acute embarrassment when issues come to light. The effects of cyber crime – whether this is ransomware that demands a payment for decryption or a theft of data that leads to fraud – are clearly challenges that cannot go unanswered; security teams are in need of a helping hand.
“The First Industrial Revolution used water and steam power to mechanize production. The Second used electric power to create mass production. The Third used electronics and information technology to automate production.”
Klaus Schwab, German Economist
Now that more automated technologies are starting to prove themselves in a number of fields, there is expectation building around the potential of AI and automation to provide the extra support needed in the battle against cyber security attackers and cyber crime.
Having the ability to leverage the emergent power of AI, the speed of automation for high volume manual processes that burden security teams and the ability to verify and triage an increasing pipeline of inputs and detections is the only way to augment the insight, oversight and expertise of increasingly scarce human operators.
However, relatively few security operations have so far adopted truly intelligent technologies that fully deliver on this promise; and are focusing solely on better detection (including through the use of AI and heuristics) or automation of manual tasks through playbooks and procedure libraries.
Adoption of AI techniques must span the full range of knowledge management, reasoning, behavioural analytics and machine-learning to deliver not only rapid threat detection but also the verification and response that today’s security teams urgently need to reinvigorate their security operations functions to keep step with the cyber crime adversaries they face.
As in past industrial revolutions, it is exactly these types of advances in AI, machine learning and behavioural analysis technologies that will be so transformative and will truly enable security systems to alleviate the pressures on their human operators.
Systems are becoming capable of learning what “normal” behaviour looks like, identifying what is significant, understanding how threats work and then making trustworthy and consistent decisions. This can be in terms of user behaviour and also in the way cyber attackers gain access and exploit systems to enable those detected threats to be validated, verified and understood automatically in real time.
This will allow security teams to automate far more of the resolution process, as security monitoring systems eliminate false positives and address a larger share of the threat management lifecycle – handling larger throughputs and with increased confidence in the decisions that are made.
Systems that call for human interaction only when necessary and provide established facts rather than simple pattern matches will free up security teams to focus on dealing with the most significant and dangerous threats in a timescale of minutes and seconds, rather than days and weeks.

This means that effort and time can be invested where they are needed most, giving security functions the edge by reducing the distraction of background noise and allowing greater focus on protecting the business.
Read by directors, executives, and security professionals globally, operating in the most complex of security environments.