“If you can measure it, you can manage it.”
Whether you are a senior executive or part of a risk and compliance audit team, you need to have visibility of your organisation’s cyber security posture. Understanding vulnerabilities using a security scorecard will allow your organisation to accept the risk or put in place an action plan for improvement.
Reducing cyber risk – knowing where to start
The question of how to obtain that visibility can leave your head spinning. With so many controls being used, an abundance of compliance obligations to meet and an array of security technologies to extract information from, where do you start?
Be smart – choose a simple process
While measuring the effectiveness of a cyber strategy is the responsibility of executives and risk & compliance teams, the operational management of the controls and associated processes themselves are the domain of the security team. All too often operations are a patchwork of individual measures and reports that have been developed over time, which makes them very difficult to assess.
Starting with a simple process is fundamental to success. We’ve all been quoted the SMART acronym through our professional careers; cyber security is no different. A strategy needs to have Specific controls, which can be Measured; they must be Achievable, which means they must also be Realistic given the resources you have. All of this needs to be Time-bound so you can track progress over time.
Characteristically, all great engineers love to explore and deliberate over new ways of doing things – cyber security engineers included. Investigating the pros and cons of sophisticated, often complex cyber security models and reports is a common past time in the industry. Most organisations do not need a high level of sophistication. Effective strategies are SMART.
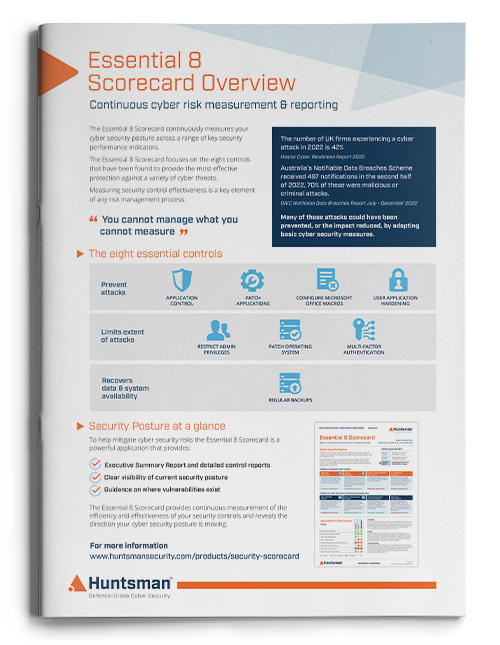
The Australian Cyber Security Centre’s (ACSC) Essential Eight mitigation strategies are testament to this. They have been proven to mitigate the most common types of targeted cyber-attacks, indeed the top four alone defend against 85% of these. You can read more about this on their website.
Measuring Effectiveness of Security Controls
To get a true appreciation of your cyber posture, the effectiveness of security controls must be tracked continuously over time. Self-assessments or even audits every few months explore a mere snapshot in time, which more often than not leaves you spending weeks and months trawling around trying to identify key metrics. Ongoing visibility is essential.
The Huntsman Security Scorecard
The Huntsman Security Scorecard was developed from two realisations:
- Around 85% of breaches stem from weaknesses in a small number of areas: patching, privileged access management and unauthorised installation of software, to name a few (see the Australian Cyber Security Centre’s Essential Eight mitigation strategies).
- Executives need to measure security as a function, alongside all other functions of the business. Security needs to have KPI’s and tangible deliverables.
How the Security Scorecard Works
The Security Scorecard gathers data proactively, collecting it to turn it into something which has real tangible meaning; identifying where there are weaknesses and how the controls are performing in the operational environment.
Cyber Metrics for your Organisation
The Security Scorecard provides executives with clear and concise reporting; a one page summary report of security control effectiveness using numeric scores and red, amber and green traffic light indicators.
For operational teams the Security Scorecard provides clear visibility of weaknesses to be prioritised. It also serves to provide continuous feedback as to whether remediation activity has been effective.
Take the first step to measuring your organisation’s cyber posture
 About Huntsman
About Huntsman