Cyber Security Predictions for 2026

The MITRE ATT&CK Framework of tactics and techniques used by attackers to probe and compromise systems is attracting a lot of attention. We’ve covered it in several blogs posts here, here and here. But is it just a framework for enterprises to manage their own low-level “root and branch” technical security? Or can it be used by MSSPs who might not be involved in that more user and workstation-centric end of cyber security monitoring?
Let’s look at the MITRE ATT&CK Framework and some ideas for Managed Security Service Providers …
Managed services often start with a small set of systems – a balance between what the MSSP would like to be monitoring and what the customer wants to spend. This might be perimeter firewalls and IDS initially as they are an effective “front line” for attacks but also quite easy for the MSSP to get access to as they are at the edge of the customer’s network.
However, the reality is – and any MSSP sales person will tell you – the more systems they monitor the better the chances of detection and the more information they can provide relating to an incident. So, if you add to that logs from the domain servers, DHCP servers, proxies, network routers and even workstations then you will get a lot more information relating to a suspicious firewall or IDS alert. You might know who the user is for a given IP address, where they are sitting, when they logged on, what files they accessed, what they did just before the network traffic started…
What MITRE ATT&CK gives you (the MSSP) is a framework for these conversations. For example if you take a MITRE technique like “exfiltration over a web service” (using something like Dropbox basically – see https://attack.mitre.org/techniques/T1567/002/) you could detect that from the firewall traffic, but if you wanted to know who the user is or where they are sitting or what files they are sharing, you need to see what’s going on at the workstation or file server. Hence you can build sales propositions based around the value of the MITRE techniques that they can provide visibility of. And the more points you are monitoring and the more data you are holding, the higher the service revenue, and the more valuable the service becomes in terms of detection and resolution.
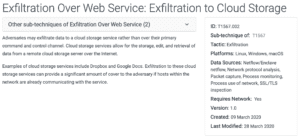
An easy technique to detect from firewall logs, but hard to resolve without knowing more about the endpoint/user/content.
When providing reports that have come from technical systems and data, that have then been interpreted by technical experts, that then get sent to, and read by, non-expert or non-technical managers can often require translation and explanation…
What is SQL injection and how bad is it? What does “pass the hash” involve? Should I be worried about this? Is a tcpdump painful?
The MITRE ATT&CK Framework allows the techniques that fall within it to be classified by the “type of goal” of the attacker and also – from left to right – you get a view of the severity, that is more than just Low-Medium-High. The spatial location on the framework shows how far along the attack lifecycle the particular scenario is.
As such, contextualising reports against MITRE is useful, but also showing where the wider spread of alerts sits can give a visual indication of how serious an event (or a series of events) might actually be. Lots of detections that create a cluster on the left-hand-side of the matrix might sound bad but could be merely probes and noise. One single alert from the right-hand-side of the matrix could be an out-and-out data loss.
When moving beyond providing monitoring services into more active (and lucrative) managed detection and response, it can be hard to frame these kinds of services in such a way that the risks of false positives become acceptable. You don’t want to disable a user account just because someone has been accessing the network from China, it could be someone who is visiting a supplier.
However, by attaching agreed responses or next steps to known and defined attack patterns and scenarios means that the risk can be better understood and the response services more tightly defined.
So, you might or might not take action against login failures or forgotten application passwords, but it’s much easier to agree that a password spraying attack (https://attack.mitre.org/techniques/T1110/003/) from a given host is a concern and should result in that network address or host being automatically blocked. Hence allowing the MSSP to offer a response service that is fully achievable for them and fully understandable to the customer is preferable.
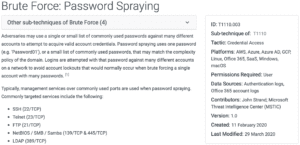
Brute Force – Password Spraying: An activity that should be blocked.
All MSSPs want to grow their business, expand their service offerings and increase the value from existing customers. Having the ability to create the rationale for this, that supports customer understanding around what those value-added services are, how they work and what the benefits are, is the trick.
MITRE ATT&CK allows these discussions to take place against a widely regarded, clear and granular backdrop. If you want to up-sell additional detection and response capabilities, tying these to a known framework that is independent means that the sales process is easier and has a greater chance of success. Moreover, it helps structure the way services are described, operated, reported on and delivered.
Read by directors, executives, and security professionals globally, operating in the most complex of security environments.