Outcome-Driven Metrics and Protection Level Agreements

Managed security services provision, or Security as a Service (SaaS), is a highly competitive market with new entrants such as IT service providers looking to add security streams of revenue or through consultancies looking to drive continuous revenue from their existing client base. It is important to understand how multi-tenancy can help.
While there is revenue opportunity the margins can be slim; especially in the early stages, when the critical mass of customers has not been reached. This post explores how you can scale your managed security services business quickly.
The two biggest cost items in providing SaaS are the technology costs for the platforms that are used to provide the service, and cost for the people to actually run it. These are intrinsically linked because the degree to which technology helps users, or avoids duplication of effort, can have a major bearing on the resource side of the equation too.
The solution to the problem comes down to reducing the ratio of security operations team members and technology platforms to customers.
Multi-tenancy SIEMs enable MSSPs to operate one single technology platform e.g. SIEM and/or Security Analytics, with a single console for multiple customers. This drastically reduces the number of technology licences required for each active customer and also means that the security team has fewer platforms to monitor or navigate around.
Multi-tenancy SIEMs house the events and alerts for multiple customers in a single central, partitioned database with ALL configurations. This means the security team operators, analysts and investigators can view all customers and complete all investigations from a single console.
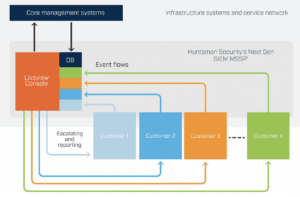
Huntsman multi-tenancy SIEM architecture
The technology costs – hardware and software – are much reduced, but the time spent logging into and out of systems, looking at separate dashboards or consoles, moving data from place to place to carry out reports is the biggest saving. Resources in cyber security are scarce enough, never mind having to manage 20 customers on 20 separate consoles, staff get burned out, there is no job satisfaction and the business doesn’t move forward.

Multi-tenancy versus federation
Some SIEM vendors seek to solve the problem of multiple standalone SIEMs by way of a federated model. A federated SIEM is where alerts are forwarded to a single central console but the events that caused the alerts to occur (and are vital as part of the investigation and compliance reporting processes) remain in the individual customer SIEMs or in separate silos. In order to investigate an alert, you need access to the SIEM it was generated in and you still have multiple points of administration and configuration.
However, there is one overarching and significant weakness in this approach, you cannot cross-correlate for suspicious activities across your customer portfolio
Put simply, this means that if you detect a threat on one customer network you can’t automatically have the system you are using look to detect that across all other customers without manually creating a rule or alert to check for it in each case.
From the customer point of view, you know about an attacker targeting systems because you’ve seen it elsewhere, yet when it hits their network it still comes as a surprise to the monitoring system.
With a multi-tenant deployment, you have a single, core platform to coordinate all security operations and service activities; you can keep customer data silos separated with their own service levels, thresholds, policies and rules – but administer them all centrally.
Plus, you can share threat data and ensure that you don’t have to reinvent the wheel on investigations that are widespread Internet problems.
It saves time, effort and provides the opportunity to offer better and more responsive services.
If you’d like to explore how Huntsman Security’s multi-tenancy SIEM has helped its customers, read the case study at: https://www.huntsmansecurity.com/resource/case-studies/developing-managed-security-services/
Fine out more at: https://www.huntsmansecurity.com/products/next-gen-siem-mssp/
See our other blog post on how multi-tenancy can also help with the onboarding of customers to a security service.
Read by directors, executives, and security professionals globally, operating in the most complex of security environments.