The second “Notifiable Data Breaches Quarterly Statistics Report” has been published by the Office of the Australian Information Commissioner (OAIC) and it certainly makes for interesting reading. The statistics within this report show a definite upward trend in reporting and interestingly it also shows a swing from last quarter’s report towards the nature of the incidents, from human error to malicious data theft. Let’s look at some of the details within the OAIC’s report and see what it tells us about the state of security within Australia.
Privacy in Australia
Earlier this year, amendments to the Privacy Act introduced the concept of Notifiable Data Breaches, mandating that organisations over a threshold of earning were obliged to report intrusions and breaches to the OAIC if they had a material detriment to individuals. The OAIC has committed to publish quarterly statistics that help businesses and government agencies better quantify the threat and target their privacy controls at the areas where breaches are most likely to occur.
Interestingly, the first report that came out three months ago showed a very different landscape to the one just released. Back then, an overwhelming majority of reported breaches occurred because of accidental release of information. However, this latest report pegs most of the breaches as malicious attacks, either as cyber security issues or as physical theft; 59% of the breaches OAIC was notified about were malicious or criminal attacks, while just 36% were attributed to human error.
OAIC received a total of 242 notifiable data breaches during this quarter’s reporting period, with the number of incidents being reported increasing month on month since the reporting scheme commenced on 22 February 2018. This shows that the word is spreading about the obligations companies have and that the first report (and the subsequent publicity) likely kicked some organisations into gear when it comes to understanding their obligations.
Information as a Target
One thing the OAIC’s privacy statistics report does very well is remind companies and individuals of their obligations and rights under this new legislation. The report also does a good job of reporting on the reality of cyber-attacks and privacy breaches in Australia and certainly helps justify spending money on risk mitigation strategies. Contact information and financial details were the two most targeted categories of data this quarter, which tallies with the previous quarter.
Most people consider these as the primary privacy information categories, given these are both used by criminals in the pursuit of criminal gain. Identity theft using personal information is higher than financial data, since credit cards, even with full details (number, expiry date, pin code and CVV), are quickly cancelled by users. Identity theft is a much more insidious issue since the data used for that crime (which can also lead to financial gain if the criminal takes out credit using someone else’s ID) cannot be cancelled like a credit card. Your identity is with you for life, so any theft of unique tax file numbers, Medicare numbers, drivers licence numbers, etc. are all a much bigger problem.
Personally Identifiable Information is low hanging fruit
This report clearly shows that most malicious hacking activities in Australia are targeting personally identifiable information, since this is the low-hanging fruit in terms of turning hacking effort into cash.
It’s worth noting that over the past few years in Australia there has been a lot of media coverage relating to hacking and large-scale cyber-attacks. Some of our biggest retailers and government departments were subject to successful hacks, some of which were attributed to criminal activity and others to overseas, nation-state threat actors, such as the Bureau of Meteorology (BOM) attack a few years ago, when the threat actor allegedly used weaknesses in BOM’s network to jump onto a more sensitive government agency. All this media coverage of hacking changed the security conversation from a holistic information security debate to a more specific cyber-security debate, where the problem (and solution) was limited to network attacks.
Now this latest report from the OAIC shows that weaknesses in physical security are as much (if not more) of a threat vector than online. The reality is businesses have spent a lot of time shoring up their cyber defences, but as the OAIC report says, “Theft of paperwork or storage devices was a significant source of malicious or criminal attacks.” Furthermore, “Human error remained a major source of breaches, accounting for 36 per cent of data breaches.”
The difference, however, is the scale of the loss. Losing a filing cabinet can see hundreds of records fall into the hands of the criminals, but a well-timed cyber-attack on a health provider’s patient database could see hundreds of thousands of records falling into the wrong hands.
The Greatest Cyber Threats
Compromised or stolen credentials, with the method of theft being unknown, is the firm leader in terms of threat vectors, with 34% of reported breaches attributed to this issue. Phishing is a close second, with 29% of attacks being directly attributed to this insidious and pervasive email threat. However, it wouldn’t be a surprise if the unknown methods of attack for compromised or stolen credentials had a high proportion of those also attributed to phishing, so both together make up the clear majority of cyber incidents reported during this period.
Unsurprisingly, health service providers were the top industry being targeted. The rich datasets containing highly confidential personally identifiable information are worth a lot on the black market. They can also be used in multiple kinds of attacks: bribery, extortion and identity theft to name just three potential crimes that can come from stolen health records.
Notifiable Data Breaches – An Indicator of Australia’s Cyber Resilience
The state of security in Australia could be better. The trends shown in this report, indicate that security is not as it should be. Many of the successful attacks are a result of simple phishing emails, which means that security awareness is deficient in these organisations.
In the background, security teams are often using labour intensive processes to deal with the millions of events pouring out of their security systems. This is exacerbated by a global skills shortage.
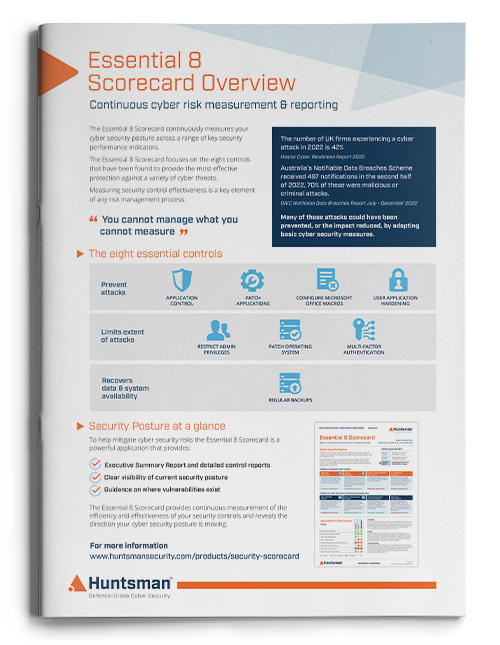
Huntsman Security has focused on making operational monitoring and alerting as easy as possible for security teams, with its Security Scorecard using the Essential Eight security controls. Research has shown that organisations that implement the controls measured by the scorecard are likely to fend off 85% of targeted cyber-attacks, so the investment is well worth making.
We’ve written other blogs on data breaches, you can find them here.
To explore how Huntsman Security can help you build your organisation’s cyber resilience
 About Huntsman
About Huntsman