Outcome-Driven Metrics and Protection Level Agreements

The latest Protective Security Policy Framework (PSPF) compliance report for the period 2017-18 was released by Australia’s Attorney General’s Department last week. The PSPF defines the Australian Government’s security classifications and associated handling protections of official information.
Of the 36 mandatory requirements across the four key areas within the PSPF including security governance, information security, personnel security and physical security, the compliance level to mandatory requirement INFOSEC-4, remains the lowest at 61.7%. INFOSEC-4 sets out the requirements for implementing cyber and ICT system security, including the Australian Cyber Security Centre’s ACSC Essential 8. You can read the full report here.
Learn why ICT system security is so important, why it is so difficult to achieve and maintain and how scorecard technology and how it can help you to start measuring, reporting, improving and tracking your organisation’s performance.
Cyber resilience, ergo information security, is a corporate business issue as it affects an organisation’s competitiveness. It is not a merely an IT task that can be set and forgotten. Businesses can be financially impacted from a data breach, which can hurt the bank account but is retrievable. However, the effect of reputational damage or national security compromises can be catastrophic and irrevocable.
The reality is that cyber resilience isn’t a race to the finish line; instead, it’s a continuous effort to respond to changes within the dynamic environment your organisation operates within. Security monitoring can identify compliant controls today that become non-compliant tomorrow; annual audits present a fleeting glimpse of security control effectiveness. Visibility of your organisation’s real-time security posture is fundamental to achieving an ongoing, robust level of cyber resilience.
The best approach to improving cyber resilience is to establish continuous security monitoring that will identify real-time deviations from your organisation’s acceptable control baseline. Does this sound like an ideal that you are never going to be able to achieve? Security scorecard technology, with its ability to continuously monitor security control effectiveness, can help your security team; even if you’re working with a limited number of skilled security staff and a modest budget.
Once established in your organisation, security scorecard technology can provide the following outcomes:
Huntsman Security’s Essential 8 Scorecard continuously collects evidence from information and log sources across the ICT environment and measures the effectiveness of security controls against each of the Essential 8’s KPIs.
The PSPF was reformed in October 2018, you can find full details here: https://www.protectivesecurity.gov.au/. Organisations will be subject to the new requirements from October 2020. PSPF Core Requirement 10, safeguarding information from cyber threats, stipulates that organisations must implement the ‘Top 4’ of the Essential 8 Security Controls: Application Whitelisting, Patching Applications, Restrict Administrative Privileges and Patch Operating Systems.
Whether you are a CIO, Risk Manager, Information Security Managers or a Security Analyst you need to have visibility of your cyber risk in order to manage it effectively. The Essential 8 Scorecard provides support for stakeholders across the organisation:
The Essential 8 Scorecard delivers automated reports that give objective metrics of latest cyber posture, maturity level against the Essential 8 Framework as well as trend reports showing performance over time.
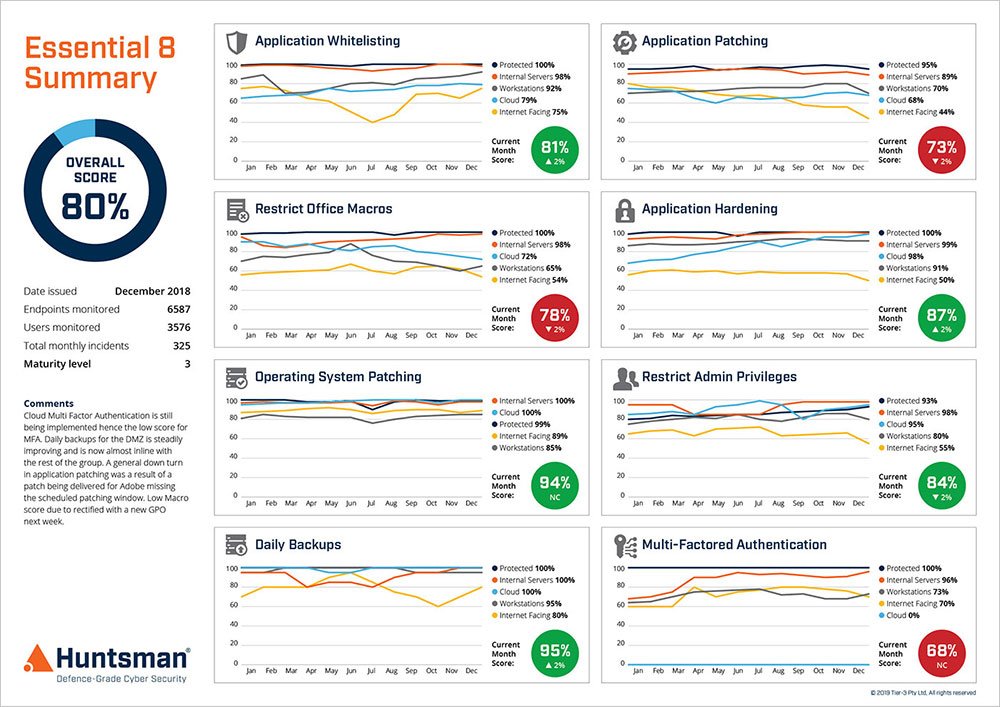
Essential 8 Scorecard – Performance Trend Report
In addition to the reports provided to management, the Essential 8 Scorecard provides reports to Information Security Managers detailing the lead-performance metrics for each of the Essential 8 mitigation strategies in relation to the Essential 8 Framework.

Essential 8 Scorecard Report
The Essential 8 Scorecard provides the cyber ops team with an operational dashboard showing real-time performance of the Essential 8 controls. In addition to the real-time dashboards showing compliance to the controls, security analysts will receive alerts about specific areas of concern. This will allow prioritisation of tasks to support the mitigation of those areas of greatest risk exposure.
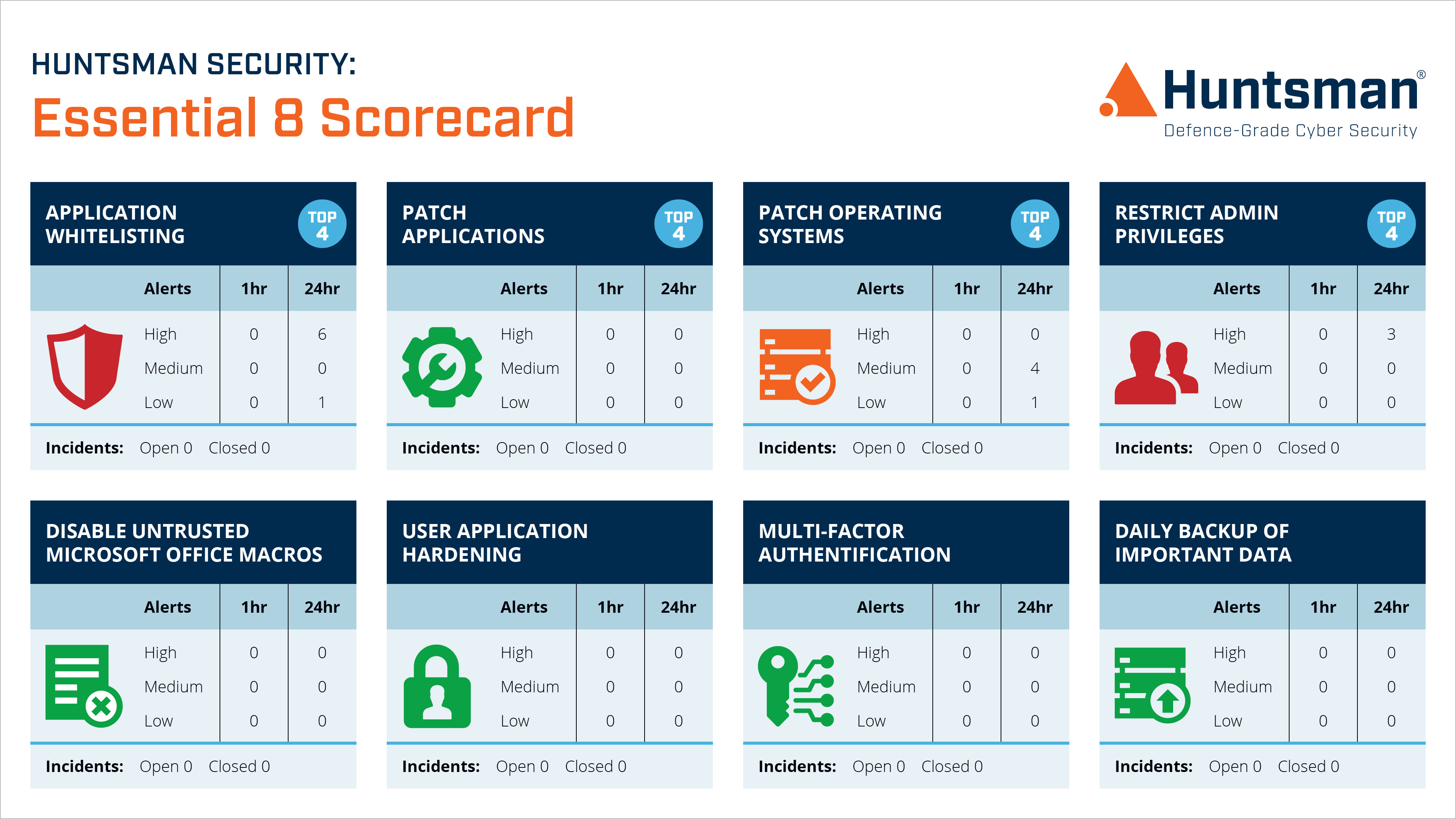
Essential 8 Scorecard – Operational Dashboard
The latest release of the PSPF is intended to embed a strong security culture and requires that each entity must report on security each financial year to:
2. Affected entities whose interests or security arrangements could be affected by the outcome of unmitigated security risks, security incidents or vulnerabilities in PSPF implementation, and;
3. The Australian Signals Directorate in relation to cyber security matters.
Self-assessment of any security control effectiveness introduces subjectivity. The Australian National Audit Office’s (ANAO) commented on their findings in their Cyber Resilience Performance Audit Report, published in June 2018:
3.15 In the absence of a common control self-assessment methodology and guidance, including a broader grading scheme, entities may continue to inaccurately self-assess and report on the adequacy of security controls.
Source: https://www.anao.gov.au/work/performance-audit/cyber-resilience-2017-18#15-0-3self-assessmentandmaturitymodel
The functionality of the Essential 8 Scorecard is founded on the ACSC Essential 8 Security Controls, a framework developed to support the ongoing resilience of Australian Government departments. The framework, combined with the scorecard technology, delivers an objective, quantitative measure of cyber risk you can rely on to benchmark, manage, track and communicate your organisation’s cyber risk.
Read by directors, executives, and security professionals globally, operating in the most complex of security environments.