Cyber security visibility, assurance and audit has never been more important – a perfect storm of increased risk and hampered delivery are weighing heavily on security audit teams.
At the time of writing the global pandemic seems far from over. US cases are still stubbornly increasing – with various states either returning to lockdown, mandating masks and/or putting a hold on the opening of schools. In the UK, the number of daily cases is now creeping back up following the easing of lockdown; the hope is that this is down to the identification of localised clusters and increased testing, but it is too early to say. Various parts of Europe are dealing with resurgences and Australia, seemingly out of the woods having fared the initial coronavirus wave well, is having to contend with an increase in cases and quarantines between states.
Despite this, in many businesses, operations are returning to normality, or a semblance of normality, with people coming off furlough schemes and returning to work – trying to pick up where they left off.
The “new normal” for security audits
No one really knows how things will pan out and what kind of “normal” businesses will return to. So, it is worth considering some of the changes and the effects they might have on the security audit and assurance processes that apply within businesses and out into supply chains.
While this transition happens, regulators are going through the same processes, resuming their previous operational levels around enforcement; data is still being handled by businesses, consumers still have expectations around security and privacy of information and laws such as GDPR still apply. A lack of regulatory attention or increased leniency during the pandemic will not last for ever. And the cyber risks, which have increased, will not go away. See https://www.cisa.gov/news/2020/04/08/uk-and-us-security-agencies-issue-covid-19-cyber-threat-update.
So what are the current and future challenges?
Cyber security and home working
It seems likely that there will be a continuance of the rise in home working. Having been forced to “make this work” during the lockdowns, there are now whole departments and operations that once occupied valuable office space that no longer need to.
Home working has a number of implications for security assurance and security audit teams. For one thing it means users are in locations where there is less control over IT, printed output, and shared access to computer systems. For security teams and information security managers, it also means they aren’t in a location where security audits or reviews can be easily conducted. Records of control operations, copies of access requests, and the ability for site inspections and audits are all significantly curtailed. This is likely to be the case for a sustained period, longer than any lockdown restrictions.
Even technical processes like network scans or vulnerability assessments might be impossible to conduct through external connections and VPNs, because done remotely they have to pass by network gateways that obstruct them and mask the results they provide.
Video conference meetings
Conducting meetings by video conferencing is now firmly established. Where once it was used only where face-to-face sessions were impossible, it is now widely accepted as the default for meetings.
This affects the way that meetings and interviews are conducted as part of security reviews and audits. In some ways, there is less personal contact with the loss of an actual, physical meeting. But the logistical time and travel costs of moving to this new way of working may mean that more “visits” and interviews and meetings to discuss security across diverse sites are possible.
People who spent (lost) a lot of time travelling or who didn’t have video conferencing facilities have been forced to adapt their own approaches in recent months.
Reduced travel
The reduction in travel, both domestically and internationally, as lock-down affects nations and prevents flying and crossing borders, has a number of implications. On the positive side, the wider adoption of working from home and video conferences should enable more in the way of security assessments to be undertaken more cheaply and with much simpler logistical planning. No need to arrange flights, hotels and travel connections for a half day meeting – now the norm would be a call or video conference.
This is particularly beneficial where there are a large number of security audits, meetings or assessments to conduct – for example in the ever-complex discipline of supply chain risk or third-party due diligence. Even a modest company can have a hundred or more suppliers. Conducting face-to-face security audits across a portfolio of companies was always a challenge.
However, the restrictions on travel makes anything “hands on” much harder: inspecting records, examining the configuration of systems, seeing the operational processes first-hand – all difficult when you can’t go and visit a site.
Luckily technology is available that fills in this particular blank. One of the areas that has seen advances in the use of automation is the provision of remotely generated audit case files data and evidence for central inspection, analysis and reporting.
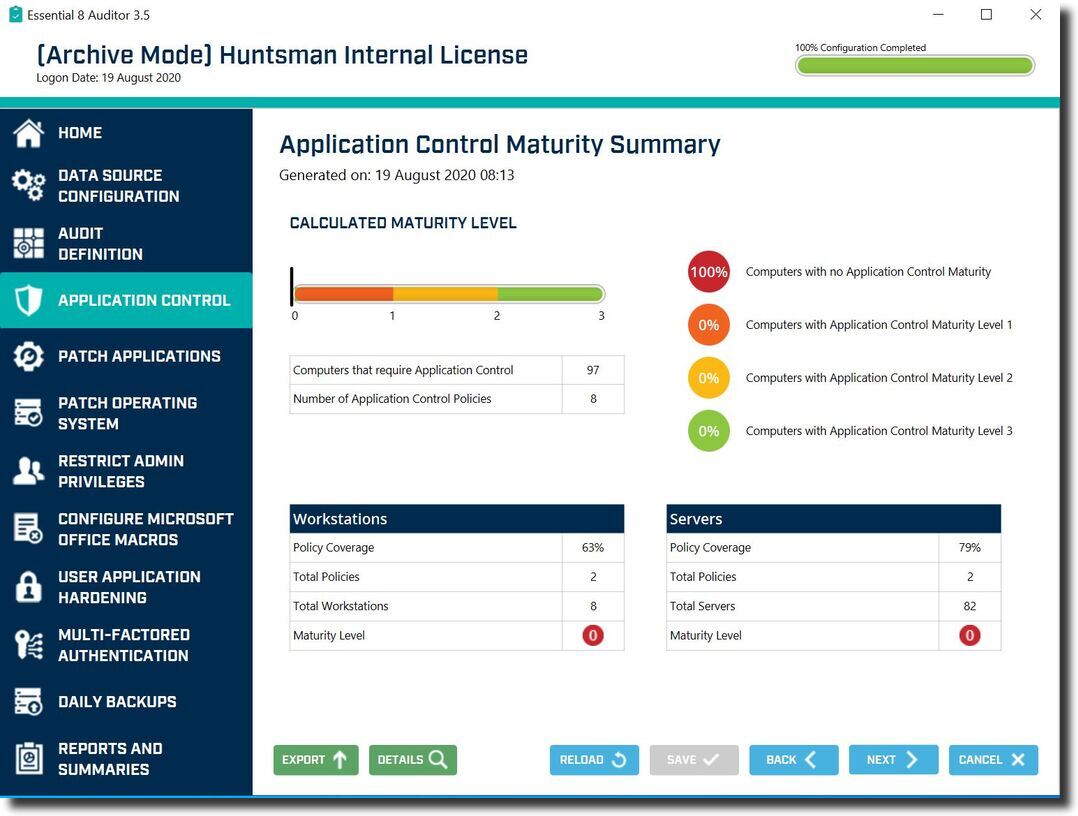
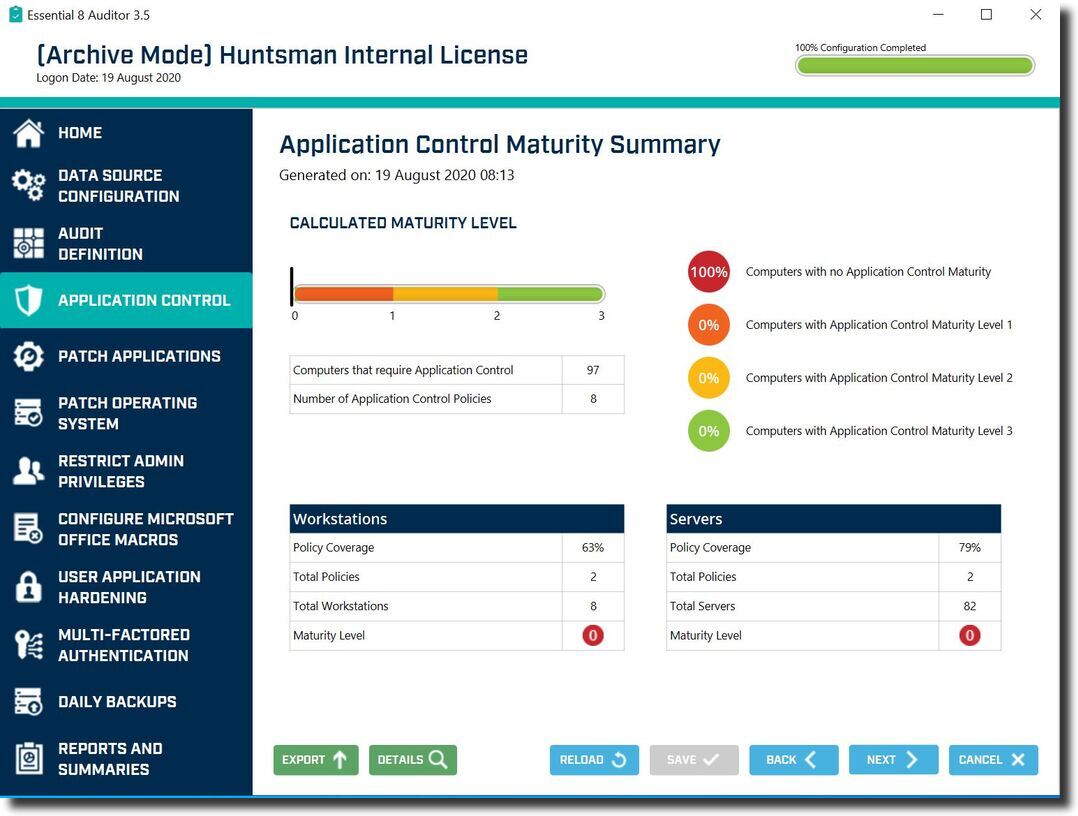
Essential 8 Auditor – Application Control Maturity Summary screen
This kind of technology allows the generation of direct audit outputs and security control effectiveness assurance in a way that would previously have needed a person to visit a site and manually examine the configuration of the security settings.
Increased use of the cloud
The trend towards the adoption of the cloud has continued to accelerate, and the pandemic has given it new impetus. The perceived security issues of taking servers and applications out of a “secure” office or data centre and moving them to the cloud were based on the fact that having direct control meant you could administer and secure them more easily. However, when it is difficult or impossible to get into office locations (and hence everything has to be done remotely) and all the users are in different places, rather than being in the same building (and hence are accessing all the platforms remotely anyway) the attraction of cloud is immense; no heating, light, rent, space charges – and wider access and utility pricing models.
This will mean that companies that have not yet fully refined their cloud security provisions and approaches, and the associated assurance and audit mechanisms, will have to elevate their capabilities in this space. It might mean they are simply catching up with more progressive businesses – but irrespective of this, the changes brought about by the pandemic mean this is no longer a choice, it is an imperative.
Continuous monitoring
The final areas where we see change are almost a result of the other effects that we’ve described above. In the past, audit programmes were constrained by logistics and so would operate on a schedule, typically annually or perhaps quarterly, as that was (a) sufficient and (b) manageable.
However, with increased levels of cyber risk arising from the revisions to business ways of working and the growth of approaches that enable more automated and less hands-on assessments, we have seen a move to augment point-in-time assessments to a more continuous model.
This recognises that a security issue may not need to persist for long to be discovered and used in an attack. Operating in a dynamic environment means that within a matter of days after an annual audit the configuration of systems, controls, accounts and the application of patches can be compromised. Having ongoing visibility not only eases the annual audit burden as data is automatically available continuously, but it also means that control failures can be picked up and resolved more quickly, and in an ongoing manner.
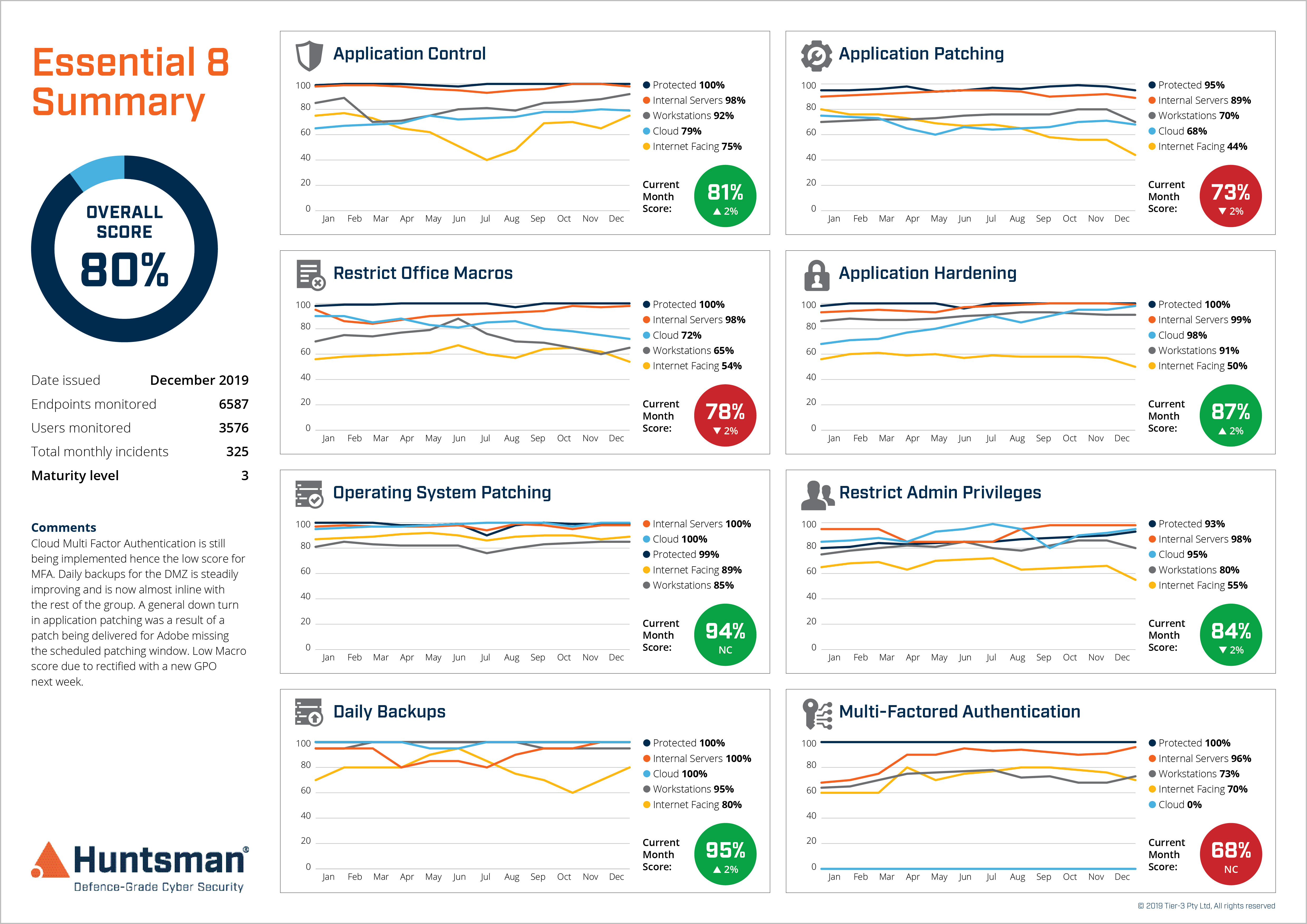
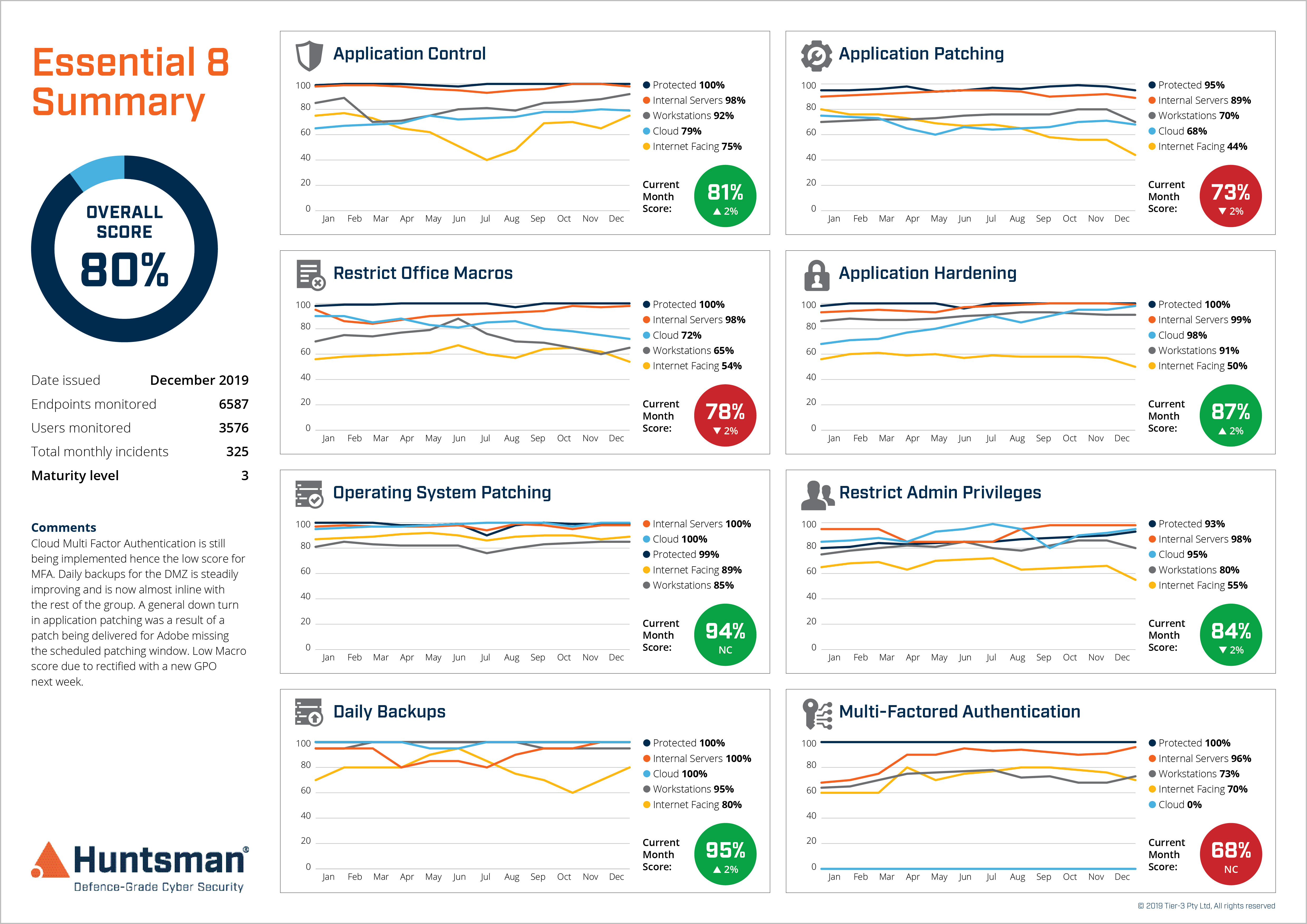
Essential 8 Scorecard – Security Control Performance trend report
The future for cyber operations and security audits
The pandemic and associated disruption for businesses may be waning, but the changes to security operations and audit are longer lasting. The good news is that many of these changes are positive and, having been driven by an external factor and the compelling event of covid-19, the delivery of security, and the oversight of it, can move into a new, more flexible, trustworthy, automated and effective phase.
Enterprises looking at their own cyber risk, and that of their supply chains, will benefit from these improvements in risk management.
 About Huntsman
About Huntsman