Security operations teams know that log management is important, yet with every operating system, network device and application writing its own set of activity-related events, how do Security Information and Event Management (SIEM) system administrators decide which security logs are important and which should be ignored. Let’s spend some time looking at today’s threat environment and from there determine a suitable answer.
Modern Cyber Threats
Most security teams know that the modern threat environment is complex and even the least capable threat actors have sophisticated tools at their disposal and can hire professional hackers to work on their behalf. Phishing and spear phishing have come a long way since the early days of bad grammar and misspelling. Many of the highly disruptive Emotet attacks recorded over the past few months in Australia have been targeted and very believable, making them more effective than ever at delivering malicious payloads. Ransomware attacks are costing Australians millions every year as attackers blend malware delivery into phishing campaigns.
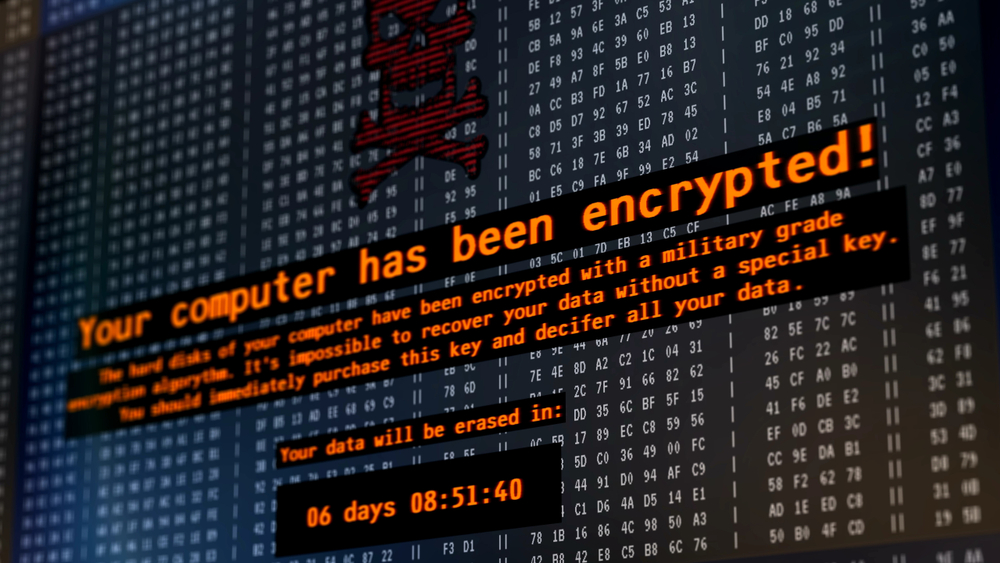
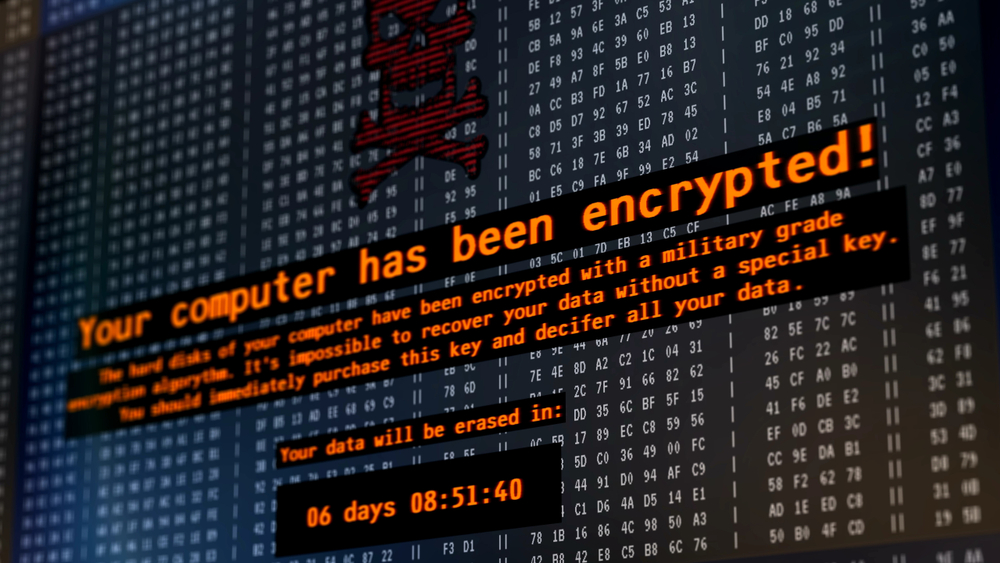
Petya cyber attack – warning message on a computer screen
Nation state attacks are also prevalent in the Australian digital economy, with attackers using their technical security and hacking skills to target state and federal governments and overrun critical infrastructure systems, which is concerning. Private sector organisations are at risk from nation states as much as government departments since industrial espionage and economic advantages are on the agendas of hostile nation state attackers. A recent example of this back in July 2020 shows how hostile nation states (allegedly Russia in this case) were using various cyber weapons, including spear-phishing and tailored malware to steal research from medical companies and research labs all around the world.
The Australian government calls on Russia to cease immediately any cyber activity, or support for such activity, which is inconsistent with their international commitments
Australian Signals Directorate, July 2020
IoT devices and autonomous vehicles are also coming under attack, as adversaries use the vendors’ haste to be a market leader to their advantage, knowing that many of these products come to market with bugs and security vulnerabilities since testing is often skipped.
Protective Monitoring
Each of these modern threats can be stopped using a combination of controls, some of which are architectural, such as network segmentation and limiting user privileges, and others which are process-based or operational, such as vulnerability management and protective monitoring. The problem is, when you start to consider each control, it’s scope and implementation maturity often extend to a larger than expected footprint, since security itself is a complex problem to solve. For this reason, protective monitoring is becoming increasingly important, since auditing and security incident management are the backbone of detecting and responding to what now seems like the inevitability of an attack.
Implementing SOC Services
A security operations centre’s (SOC) primary purpose is to monitor the organisation’s systems and applications for signs of abuse and respond to cyber incidents. Modern SOC architectures rely on technology such as SIEM tools and service management platforms to detect indicators of compromise (IoCs) and coordinate a response across the stakeholders, ensuring the right procedures are taken to quarantine threats and recover from the attack.
Security Logs
SOC teams have struggled for years to determine which events to gather from log sources, since looking for IoCs is akin to searching for the proverbial needle in a haystack. Digital environments are known to produce a deluge of useless information and only occasionally provide the security-relevant events needed to detect an attacker. However, with the rise in sophisticated nation-state attacks and highly evasive malware, how can SOC teams decide which events and security logs to keep and which to throw onto the digital rubbish pile?
Modernised SOC Operating Model
We know that attackers continually refine their tactics and techniques to compromise their targets, rendering SOC teams that rely solely on traditional signature-based detection measures blind to these sophisticated threats. Nation state attackers employ highly evasive malware incorporating novel techniques and zero-day vulnerabilities that make the job of defenders harder than ever. The consequence of nation states upping their game and shifting to a more sophisticated adversarial model is that SOC teams need to do the same. But what does this mean to their existing operating model?
Collect all security logs
In terms of the data collected by the SOC, it needs to shift to a new approach that doesn’t differentiate between useful and useless security logs. Highly evasive attacks may well be undetectable using today’s knowledge and threat intelligence, yet given a few days or weeks, they may be discoverable. Therefore, rather than discerning which events are useful in advance of knowing how the attacks work and sink holing the rest, SOC teams are shifting to log all events coming from operating systems, network devices and applications, including cloud-based solutions and IoT systems.
Since it’s impossible to know what every suspicious activity looks like, then the whole body of auditable data produced from your enterprise is needed to properly search for and build rules for detecting threats. What might seem like an innocuous or unnecessary event today may be the artefact needed tomorrow to build a more effective correlation rule. Furthermore, given the advancement in machine learning and artificial intelligence in SIEM platforms, building a baseline of known behaviour to allow the system to report suspicious anomalies is only possible when you collect everything. Is there a reason why collecting all these events is not possible?
A solution that can help
Huntsman Security’s Next Gen SIEM includes Behavioural Anomaly Detection (BAD), to detect unknown and unknowable threats. The platform relies on collecting all the data from your environment so the modelling algorithms can build the picture of what normal looks like. Using this baseline, BAD can provide insights and detections based on suspicious looking activity, whether by users, machines or applications operating across the network, and allows the SOC team to investigate and resolve attacks that otherwise would have been missed.
Undoubtedly, the threat environment has changed and what worked five years ago may not be effective for what we need today. Modern technology platforms can help. To discover more, please don’t hesitate to contact the Huntsman Security engineering team:
 About Huntsman
About Huntsman