Outcome-Driven Metrics and Protection Level Agreements

This blog post “CMMC – System and Information Integrity’’ is the seventh in a series on Cybersecurity Maturity Model Certification (CMMC) – a US Department of Defense (DoD) initiative that imposes requirements on contractors and subcontractors to help safeguard information within the US defense supply chain.
In this post, we look at some of the ways you can achieve a higher level of maturity in the system and information integrity domain to ensure important operating system files remain unharmed and malicious software is blocked from executing on your computers.
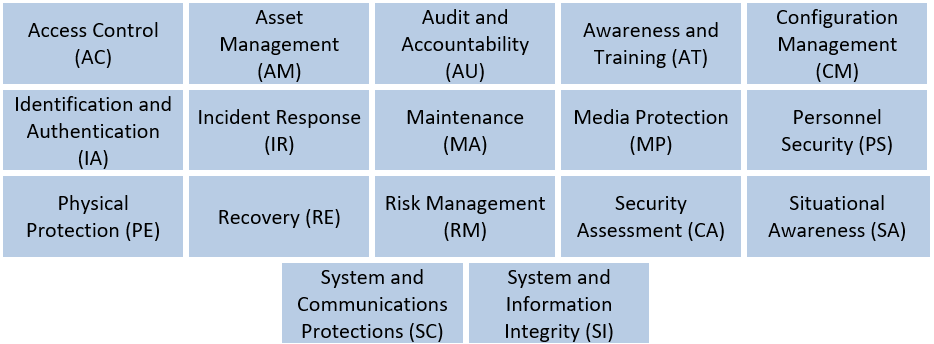
CMMC Domains
The Australian Cyber Security Centre (ACSC) promotes eight critical security controls to protect government systems, known as the Essential Eight. The top recommendation within the “Mitigation Strategies to Prevent Malware Delivery and Execution” category is Application Control, otherwise known as application whitelisting. Application control prohibits the execution of unwanted executables on computer systems, thus preventing malware in the form of .EXE files, .DLL files and various forms of script from executing. Application control is a powerful way to protect your systems and makes infection from traditional malware and hacking tools very difficult.
Within the CMMC there is a requirement for protection from malicious code at appropriate locations within the organisation’s information systems. This requirement refers to being selective about how you deploy application control, so that you choose designated locations to enforce these rules, such as system entry and exit. Entry and exit points refer to gateway systems as well as firewalls, VPN servers, email systems, webservers, and mobile devices (including laptops and tablets).
CMMC is specific about identifying the types of malware the organisation should defend against, naming viruses, worms, Trojan horses, and spyware as the most important. It also points out that malware can be hidden in encoded payloads, using techniques such as UUENCODE and Unicode, as well as being masked within a compressed file or stored on the hard drive as hidden files or disguised using steganography or alternate file streams.
It’s also important to consider the method by which the malicious code may be installed on the system, since it could arrive through a user’s web accesses, via email (a linked URL or as an attachment), and through a user plugging in an unauthorised USB storage device.
CMMC discusses the need for holistic configuration management and asset control, hence the need to review and ensure your software integrity controls are effective. An example of this would be to ensure that only authorised applications are installed on user workstations, by having an authorised inventory list and then periodically auditing the installed applications on the endpoint. Automated application control does this, however, you can also do it manually.
Viruses and malware can also be introduced into an environment through interference from malicious insiders, who may even have the IT skills to develop their own custom-built hacking tools. The kinds of malicious code you need to consider when looking at suitable security controls include, as CMMC points out, “logic bombs, back doors, and other types of cyber-attacks that could affect organizational missions/business functions.”
The problem is, traditional antivirus systems rarely have the intelligence to detect and quarantine these kinds of threats, since they rely almost solely on signatures (a digital fingerprint of a file that is impossible to forge), which are of no value when we are concerned about newly built malware. In these cases, CMMC recommends that you introduce security controls into your software development practices, where code is checked for backdoors and logic bombs by an independent code reviewer, and access to compilers and other such software build environments is controlled via policy so that only authorised developers can access the development environment, and they have no ability to deploy code directly from the build environment into the production environment.
Furthermore, the release process should include a variety of tests to improve the efficacy of the code review, where you can do automated secure code testing, a vulnerability assessment and load testing. You can also tighten up your configuration management and software distribution processes so that only trusted sources of applications can be used to deploy software, and those sources are also tightly controlled by a team of trusted (security cleared) software distribution experts.
The final control worth mentioning is Protective Monitoring, as it helps with incident management and incident response. It ensures any of the security controls you have introduced report appropriate logs to the security team, and they can act upon them when they see issues. Furthermore, making the security team the coordinating point for all of these processes ensures commonality in how things are monitored, so that even in-house developed software includes the requirements to log application usage and you can look for patterns of misuse that could indicate either a user or the application misbehaving.
Feeding all of the security logs into a Security Information and Event Management (SIEM) system allows the security operations team to build special rules of their own to detect known attacks, and also record baselines of what normal software operations looks like, so that unusual behaviour (known as anomalies) is quickly brought to the attention of the security team.
Next generation SIEM technologies, capable of both correlating known attacks and building behaviour baselines that allow organisations to detect threats as network and system anomalies, are most helpful in maintaining system and information integrity.
Essential 8 Scorecard – Security Control Performance Tracking
You should also look at security scorecard technologies that monitor and report on security control effectiveness, so you can quickly see when key mitigation strategies, such as Application Control, are no longer protecting the business as they should.
Read by directors, executives, and security professionals globally, operating in the most complex of security environments.