Cyber Security Predictions for 2026

The Federal Court recently provided guidance on what constitutes adequate cyber security protection for licenced Australian Financial Services (AFS) providers.
For security leaders, risk professionals, and executives, the message is clear: cyber security is no longer just a technical function. It is an ongoing enterprise governance, risk and resilience priority.
On 13 February 2026, the Court handed down its judgment in ASIC v FIIG Securities Limited, ordering the AFS licensee to pay a $2.5 million penalty for failing to implement adequate cyber security protection.
While this case sits within financial services, the implications extend far beyond. It establishes a practical definition of “adequate” cyber security that applies across all sectors.
The ruling highlights four critical principles for achieving adequate cyber security protection for organisations themselves and their customers:
From these principles it follows that as cyber security standards change, the balance of technical resources and skilled personnel is likely to change as organisations seek to improve their cyber security operating models to maintain adequate ongoing protection.
The Court identified three essential components of adequate cyber security protection:
While preventing every cyber-attack might be impossible, the Court expects organisations to have adequate cyber security protection. “Adequate” being a context specific term, rather than definitive; implying that cyber security protection standards will vary depending on the nature of cyber security threats faced.
The adequacy of cyber security protection should consider (and regularly review) the risks that are relevant to the specific organisation and its operations:
Many organisations are currently struggling with the complexity of their cyber security protection. The Court acknowledged that effective protection relies on the interdependence of security controls, risk management systems and adequate resourcing.
In ASIC V FIIG, shortcomings in resourcing contributed directly to inadequate cyber security outcomes.
Technical capability and specialist expertise are essential not only for implementing controls and risk management systems, but for maintaining their effectiveness over time. Without access to relevant and up-to-the-minute security data, its interpretation and expert oversight, the cyber security protection process quickly becomes arbitrary and unsuitable as a decision-making or management tool.
Rather than a definitive list of required cyber security measures or controls, the Court identified a number of observed shortcomings (see 20-42 in Court Judgement). No direct advice was provided in relation to a particular cyber security framework that might assist in the definition of adequate cyber security measures.
Although, a quick reference to the ACSC Essential Eight framework reveals more than a passing similarity between the measures listed by the Court and the ACSC Essential Eight Maturity Model controls.
An adequate risk management system should implement, maintain and manage the controls necessary to protect the organisation and its clients.
The Court noted that adequate risk management systems are dependent on:
Increasingly, as cyber security becomes another operational risk for enterprise to manage, the integration of cyber security into broader enterprise risk and resilience activities, supported by new inter-disciplinary operating models, will be required to better coordinate technical and risk functions.
The balance between technology and human resource investment within the cyber security protection process is changing. Disconnected processes and a lack of skilled and knowledgeable cyber security personnel, as evident in this case, can seriously impact cyber security outcomes.
At the same time, organisations are facing increasing demand for timely, reliable and evidence-based security information to support decision-making.
In a rapidly evolving threat environment, an inability to maintain effective cyber security protection can quickly impact operations and overall enterprise resilience.
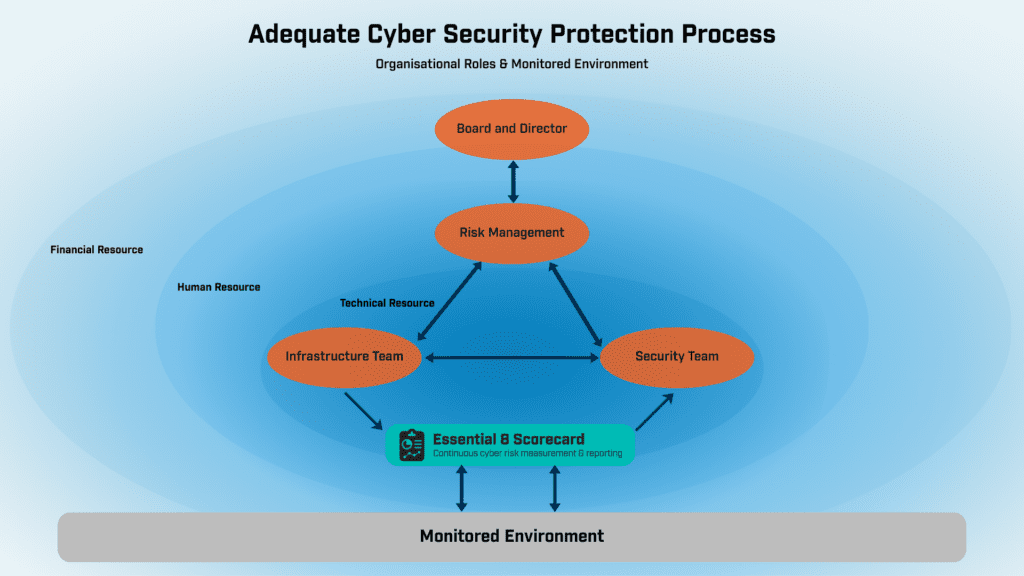
Effective cyber security risk management brings with it some challenges – threat velocity, visibility, impact and time to response, to name a few. Newer operating models like that in Fig 1.0 (see below) are addressing some of these challenges.
Effective cyber security protection processes need to be agile and dynamic to meet the sometimes urgency of cyber security risk management in a volatile and dynamic threat environment. As a result, the cyber security protection process increasingly requires the collaboration of multi-skilled participants and information flows – technical, cyber security and risk teams – to quickly and reliably detect, analyse and mitigate emerging security risks before they can impact enterprise operations.
All rights Reserved © Tier-3 Pty Limited 2026
The judgment reflects a broader trend: cyber security is becoming more complex, while resource constraints and siloed operations remain a persistent challenge.
As a result, organisations are increasingly seeking technology that can supplement human expertise and provide more immediate, data-driven insights.
Continuous measurement of control effectiveness, near real-time risk identification, and automated reporting are becoming essential components of modern cyber security. These capabilities enable organisations to maintain adequate protection even as the threat environment continues to evolve.
The ASIC v FIIG Securities decision makes clear that adequate cyber security is not defined by controls alone. It requires an ongoing, integrated approach that combines effective measures, informed risk management, and the right balance of resources to maintain adequate cyber security protection.
Organisations that fail to adapt and appropriately resource more responsive risk management systems will continue to suffer, not only regulatory consequences, but also broader impacts to their operations and enterprise resilience.
Strengthen your cyber security protection
Maintaining adequate cyber security now requires continuous visibility, control assurance, and risk-informed decision-making.
Huntsman Security supports organisations by enabling that continuous monitoring of control effectiveness for near real-time threat visibility and active cyber security risk management systems.
Read by directors, executives, and security professionals globally, operating in the most complex of security environments.