Outcome-Driven Metrics and Protection Level Agreements

Security risks are prevalent in most organisations, yet the consistent management of all technical, process and personnel-related security problems can be difficult as multiple teams are often identifying and mitigating them. In a bid to address this, many organisations are now fusing their risks management technologies and approaches into one Integrated Risk Management (IRM) solution comprising the platforms and processes needed to unify this critical business function.
IRM solutions – give your business full visibility of the risks
IRM contains all the features an enterprise risk management approach needs to deliver strategic, tactical and operational management of risks, combined with the tools and processes for identifying and mitigating them.
When evaluating what IRM means to your business, you must consider the things that matter most to each of your stakeholders: the board, the management teams and operational staff. Executives want to see the big picture, with accurate reporting across the entire business so they have the visibility of what’s immediately relevant to them in terms of mitigation investment.
At the middle management layer, risk-based decision making is essential. Having the information needed to fully understand tactical and operational risks and prioritise remediation plans within the workload pays dividends.
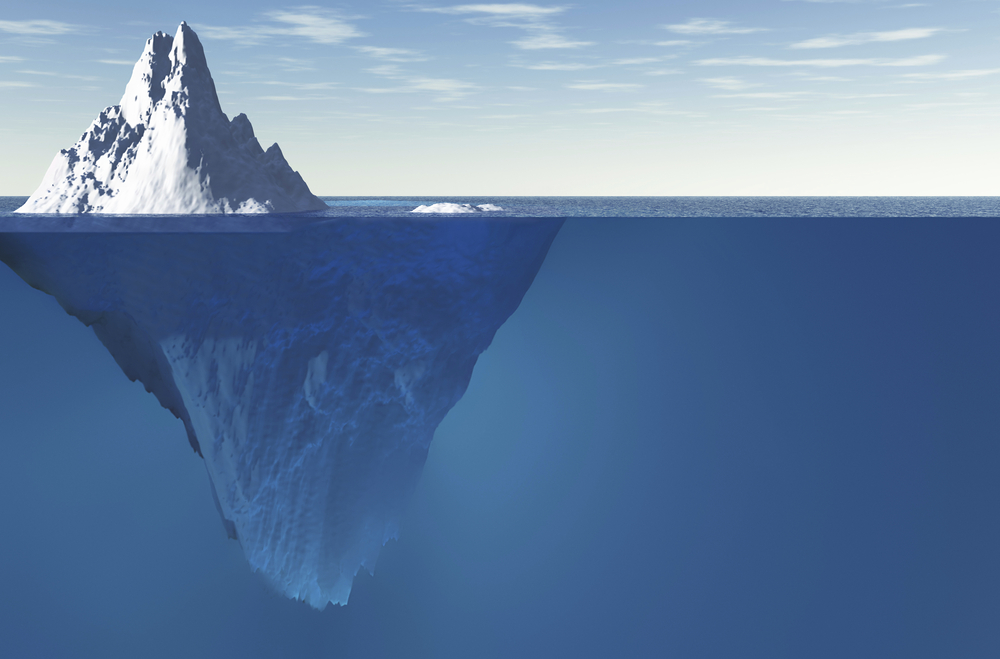
As your business changes over time through organic growth, customer acquisition, mergers and acquisitions or the introduction of new product lines, removing the risk management siloes that teams have built up over the years is vital. New risks are always appearing in the business, and even if they are technical risks, they can have a negative strategic impact on the business’s wellbeing. Two words help people understand this challenge: data breach. A low-level technical vulnerability in a simple wifi access point could be the issue that leads to the theft of your customer database.
IRM supports the business need to communicate risks, no matter their provenance, to the right audience, enabling better and more robust decision making. IRM also gives risk management owners a greater understanding of the nature of aggregated risks; where risks are chained together to raise their ratings higher because as a collection, they demand a faster response and a more comprehensive mitigation plan than any one of them individually.
Cybersecurity risks are often considered strategic by the business since they are on today’s boardroom agenda. However, these security risks tend to originate from technology platforms, so IRM systems need to aggregate them from operational systems using monitoring and system management systems, such as tools for vulnerability assessment, antivirus, SIEM, configuration management and, software distribution.
An IRM solution should fit with your organisation’s needs
Before you rush out and buy an Integrated Risk Management solution, you need to carefully consider how you get buy-in from all of the relevant business stakeholders and associated risk management teams that would use it. This includes understanding the methods, processes and tools they use today to meet their local risk management objectives. Don’t look to mimic all extant business processes or approaches to management risks found in each team, since a critical review may expose better and more efficient or accurate ways of identifying and reporting on key risks to the business.
Spend an appropriate amount of time defining all your business requirements so the solution is comprehensive and meets the needs of operational, middle management and executive teams. Also, consider how you identify IRM champions across the business to help with implementation, since some areas of the company could be very parochial or remote. You need supporters on the ground who can institute the new processes and platforms and train people who need to use it.
If you don’t have the in-house skills or experience to design an IRM solution, you should seek outside assistance. IRM is one of the most critical business systems to invest in over the next few years, and because of the complexity and highly-integrated nature in the enterprise, it needs to be comprehensive and streamline. If the solution only makes users’ day jobs harder or makes them less productive, possibly because they don’t understand it and are not trained, the solution could fail from the start.
Integrated Risk Management adoption is essential. It would be best if you supported this complex business processes change with a comprehensive rollout plan that includes communication and training.
IRM solutions don’t have to be single-vendor systems. A well-integrated approach, using the best tools for the job, is often better than trying to use one technology for everything.
In cybersecurity, we use vulnerability management platforms to gather patch-state information and configuration data from ICT systems and report those against a database of known bugs and issues. Results reflect how easy it is to exploit a vulnerability, and then it’s the business’s job (usually the information security management team) to explain those risks in the context of the enterprise infrastructure – security architecture, processes, protective monitoring, physical security and business continuity measures – considering compensating controls and mitigations. If mitigating the risk requires investment, you may need to elaborate on its context for middle managers and executive managers, so additional context against strategic business plans needs considering.
An IRM system would not replace the vulnerability management platform, instead it would take the output of that expert system, allow the security risk manager to annotate the risk and modify it with context and provenance. The solution would build this into a dashboard or present it in a way that makes sense at the next level up within the business. Ideally, when the security manager submits a risk that is above the set level of acceptance, it should be brought to the attention of the teams who have the authority to treat it.
Lastly, if you can integrate the risk management system with your service management platform, you can incorporate a proactive approach to managing incidents. By giving historical visibility to the processes involved in incident management, linked to the root cause analysis, you begin to infer where risk-based decisions may have been wrong so that the course is corrected next time.
IRM is the future of enterprise risk management. It pays to get on the front foot and begin looking at how you identify operational risks and give them strategic context. Only then will business leaders be able to rationalise low-level technical security risks (vulnerabilities and configuration issues) with their strategic planning.
Read by directors, executives, and security professionals globally, operating in the most complex of security environments.