Outcome-Driven Metrics and Protection Level Agreements

Managed security services is a fast growing industry and nearly every MSSP we talk to is looking to drive growth through the acquisition of new customers. However, making this growth profitable and scalable relies heavily on the capabilities their technology platforms have in a specific area – Multi-Tenancy.
The SIEM and Security Analytics markets are relatively mature, with many available solutions being 10+ years old. Most solutions were designed for on-premise deployment for a single customer. As such they are expected to be set-up and configured once only.
By contrast an MSSP needs to minimise overhead when onboarding each new customer and to be able to manage many customers from a single SIEM via a single console. They need to deploy the core technology once (as per an enterprise) but then add “deployments” as they attract new customers to their service.
The repeated set-up and configuration of the software is the hidden cost of SIEM technologies that are not multi-tenanted.
With a stand-alone or even federated solution, on-boarding each new customer is like starting from scratch every time; you need to deploy the software, configure rules, alerts, dashboards and reports.
A multi-tenancy SIEM solution, only needs to be set up once, for the initial SOC platform and/or first customer. Any additional customers use the configuration that’s already in place (perhaps with some customisations). This means you can house 20-30 plus customers on a single platform giving lots of additional savings and the ability to grow revenue faster.
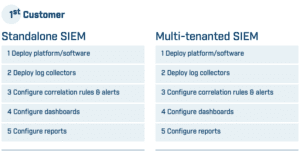
The steps involved in building the core SIEM platform and accepting the first customer is the same, whether you use a standalone SIEM or a multi-tenancy one:
But for every customer after that, it is very different. A multi-tenancy SIEM skips a number of the steps, saving a significant amount of time and effort for all additional customers:
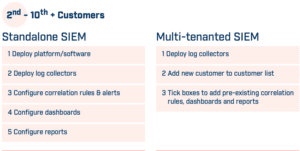
If the growth plan for your managed security services business is to add 10/20/50 or even 100 new customers, then the operation needs to be scalable.
If the configuration of each new customer takes 1, 2 or 3 days it’s easy to see how this can build up and potentially delay the commencement of services (and hence revenue). It could also pull engineering resources away from other tasks or disrupt the operation of the security services for other customers.
Again, and again we have found that multi-tenancy is the key reason that MSSPs switch to our SIEM; having a scalable multi-tenancy SIEM is fundamental to providing a successful managed security service.
We have a case study at: https://www.huntsmansecurity.com/resource/case-studies/developing-managed-security-services/
Visit the product page at: https://www.huntsmansecurity.com/products/next-gen-siem-mssp/
See our other blog post on how multi-tenancy can also help with the ongoing operation of a security services.
Read by directors, executives, and security professionals globally, operating in the most complex of security environments.